Managing access rights of privileged users is one of the cornerstones of data security. That’s why the privileged access management (PAM) market is booming with tools and practices. But this variety of PAM options makes it challenging to figure out which practices and controls your organization can benefit from.
To help you choose the best practices for privileged access management, we’ll overview six essential PAM controls required by IT compliance requirements as well as five advanced practices to ensure stronger access protection in complex and diverse infrastructures.
Why is PAM important?
Privileged accounts are often involved in security incidents, with or without malicious intent. A user can cause an incident unintentionally by neglecting cybersecurity rules and, for example, visiting shady web resources or downloading suspicious files. Also, if hackers gain privileged credentials, they will be able to interfere with an organization’s systems and data.
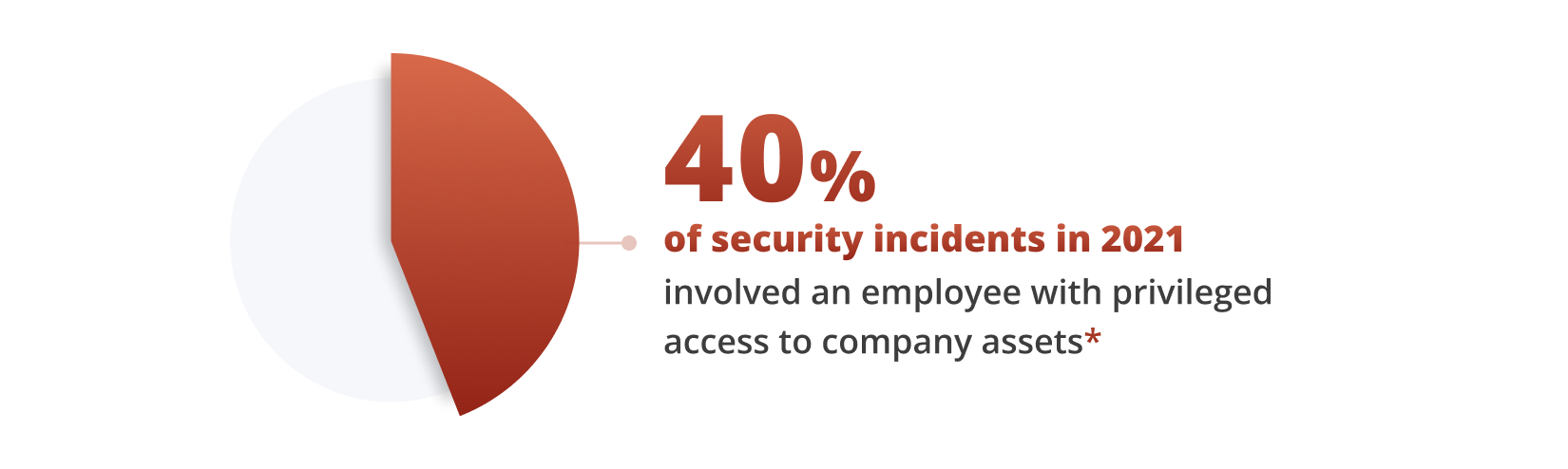
*Data from the IBM Security X-Force Insider Threat Report
Privileged access management is a set of tools, techniques, and practices that allow organizations to mitigate security risks related to users with elevated access rights. Gartner Peer Insights (subscription required) states that “PAM helps organizations provide secure privileged access to critical assets and meet compliance requirements by managing and monitoring privileged accounts and access.
In particular, privileged access management tools and practices allow you to:
- Discover privileged accounts
- Manage privileged user credentials
- Control access to privileged accounts
- Monitor and audit privileged access sessions
- And more
Adopting PAM practices not only helps organizations improve their cybersecurity posture but also provides the following business benefits:
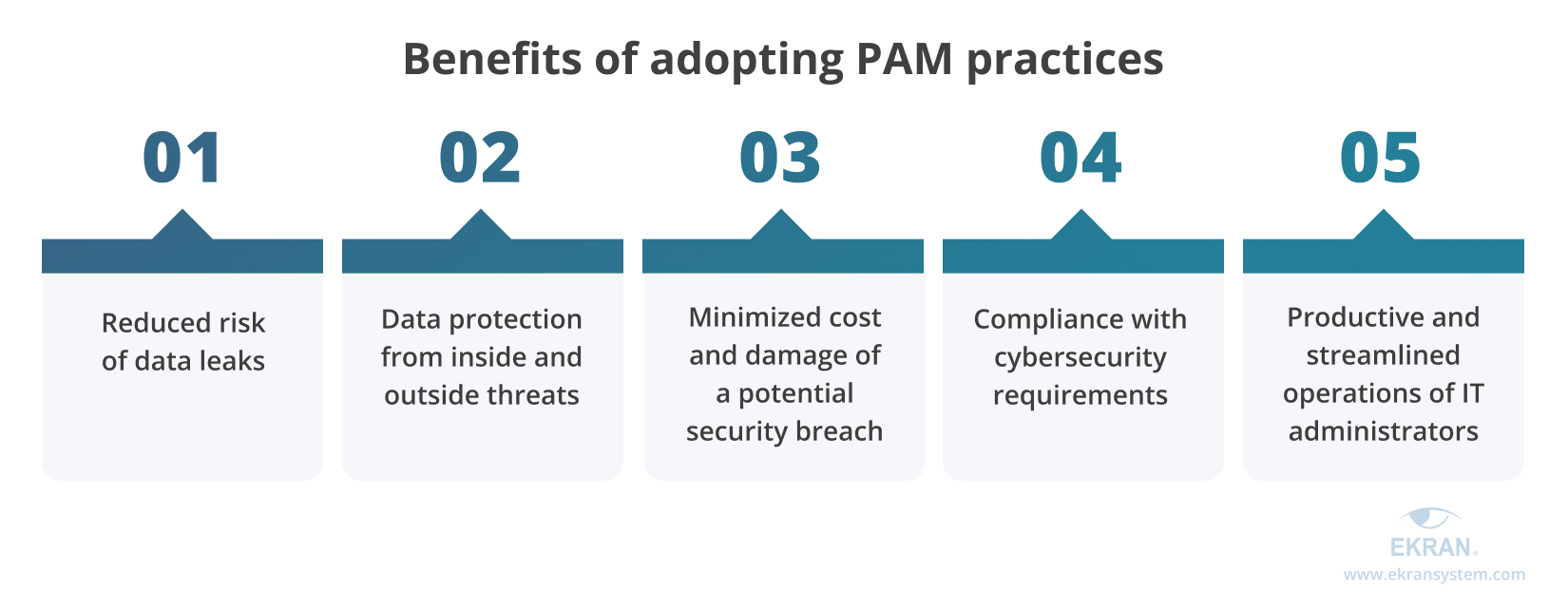
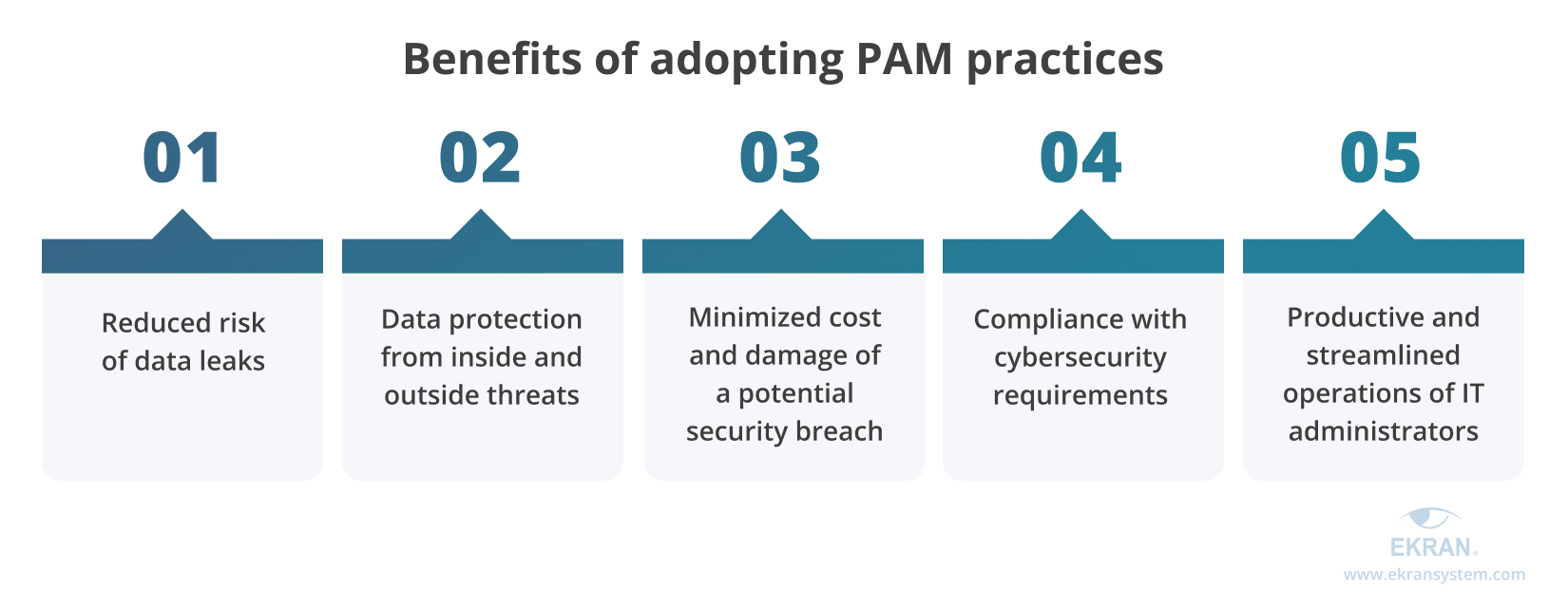
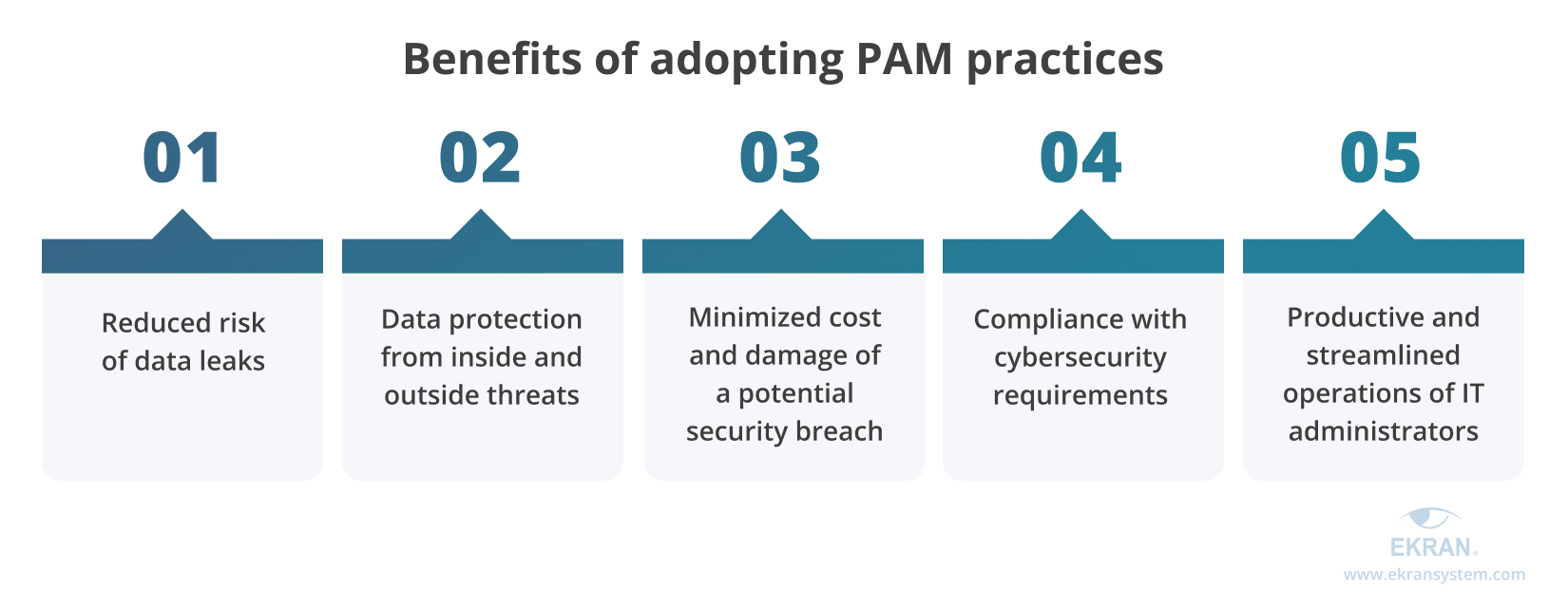
The benefits of and increasing need for the protection of privileged access are driving the rapid development of the PAM software market. In 2020, it was valued at $2.47 billion and is expected to grow to $19.37 billion by 2030, according to Allied Market Research.
Such a huge and diverse market offers numerous tools, solutions, and approaches for access management. That’s why it can be challenging to choose practices you need and implement efficient privileged access management in your organization. In the next section, we examine how to choose relevant privileged access management best practices and which are considered must-haves.
6 basic privileged access management practices
The best way to choose relevant PAM best practices is to research which privileged access management controls are required by key cybersecurity laws, standards, and regulations. The list of IT compliance requirements to follow varies for each organization.
Usually, it depends on an organization’s location and line of business as well as the nature of sensitive data the organization processes. However, it’s safe to say that the majority of organizations have to comply with NIST SP 800-53, GDPR, or ISO 27001. They include must-have controls and practices to securely manage privileged users.
Here are the key access management practices these standards and regulations include:
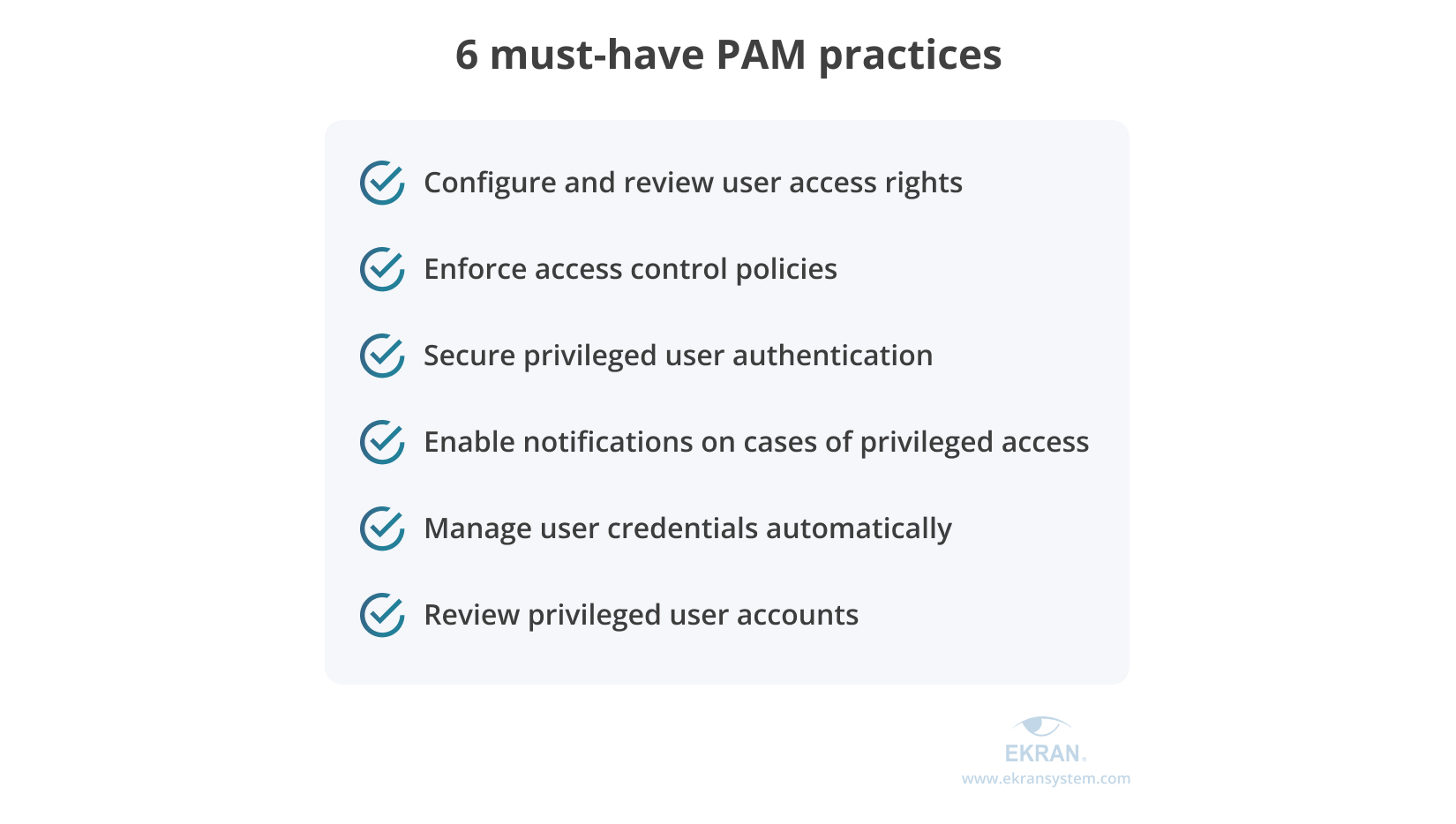
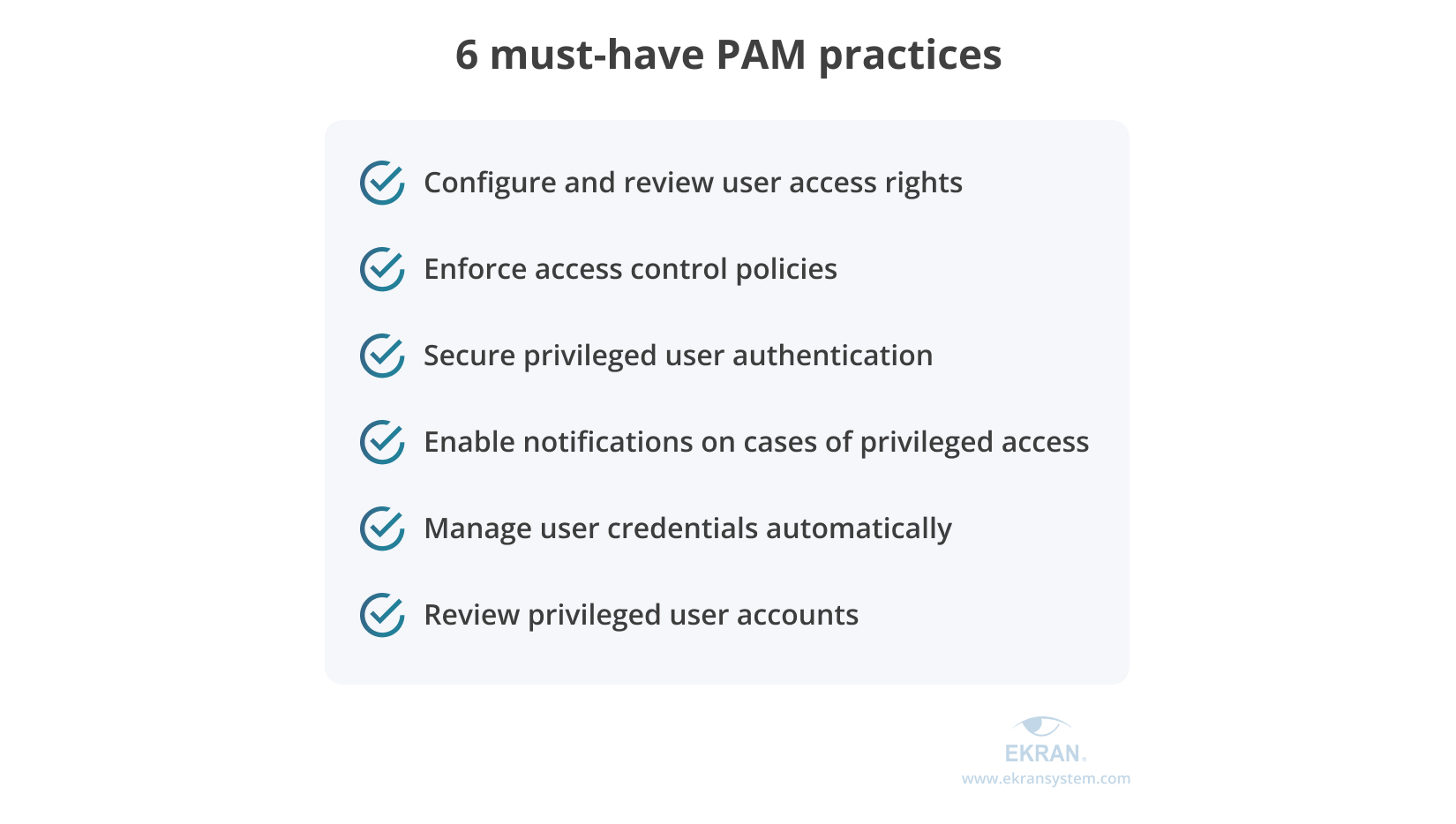
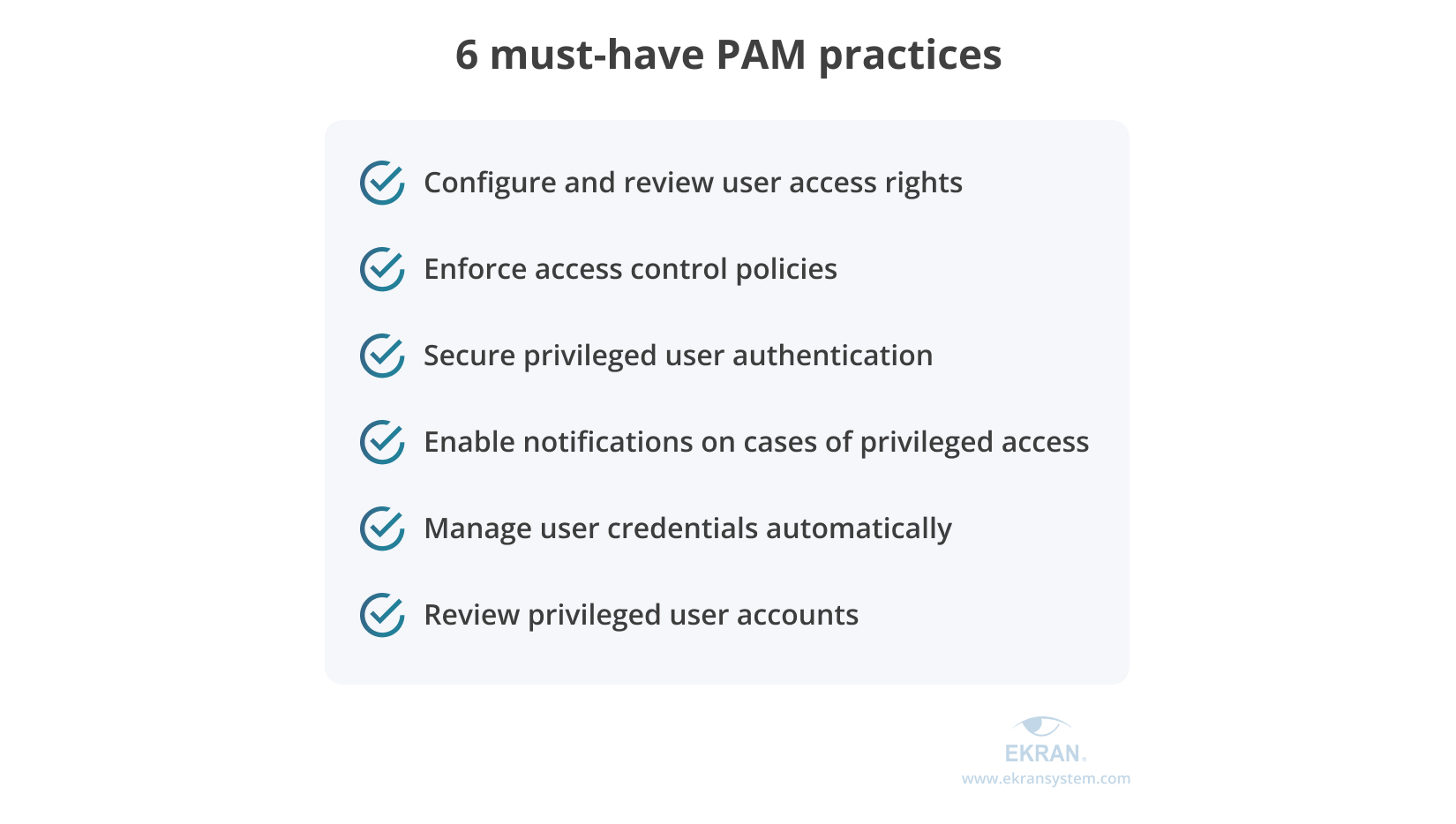
1. Configure and review user access rights. Make sure to assign each user only those access permissions they need for their work. Security officers should be able to granularly configure privileged access for users and user groups, as well as review and revoke previously granted access permissions. This way, your organization can avoid privilege creep and limit the possible attack surface.
2. Enforce access control policies. A company-wide access management policy clearly defines who can access which resources under what conditions. Making your organization follow a single strict and detailed policy makes access management procedures transparent and efficient for both regular and privileged users.
3. Secure privileged user authentication. Theft of a privileged account is a common entry point for malicious actors. You can protect privileged accounts by adding multi-factor authentication (MFA) to their login procedure. MFA checks something a user knows, the user’s biometrics, or something the user possesses before providing privileged access.
4. Enable notifications on cases of suspicious privileged access. Security officers have to keep an eye on unusual requests for privileged access. But since it’s impossible to control all access requests, they also need a tool to stay alert to high-risk and suspicious requests. Security officers should be able to configure custom notifications for specific cases.
5. Manage user credentials automatically. Hackers can brute force an account or use social engineering to obtain a privileged user’s credentials. Also, users can simply use weak passwords or the same password for lots of accounts. Automating credential management with dedicated identity management software helps to rotate credentials, prevent users from creating weak passwords, and make credential leaks almost impossible.
6. Regularly review privileged user accounts. A periodic review of privileged accounts is required to discover inactive accounts, unneeded privilege escalations, and unprotected system and emergency accounts. This way, security officers can detect and secure potential hacking points.
These access management best practices satisfy the basic requirements for securing privileged access and complying with IT standards and regulations. However, large enterprises and organizations that deal with lots of sensitive data and have complex infrastructure may need more flexible or advanced practices. Let’s take a look at some of them in the next section.
5 advanced access management practices
Advanced access management practices help security officers simplify access management procedures, adjust them to the needs of their organization, and make security more flexible. However, they also are more challenging and costly to implement than the practices we discussed in the previous section. So before adopting advanced PAM practices, determine if you really need them and which security issues they will solve for you. Also, compare the cost and effort of deploying these tools with the benefits you’ll get from them.
If you decide that your organization does need to enhance its access management capabilities, consider adopting the following practices using Ekran System functionality.
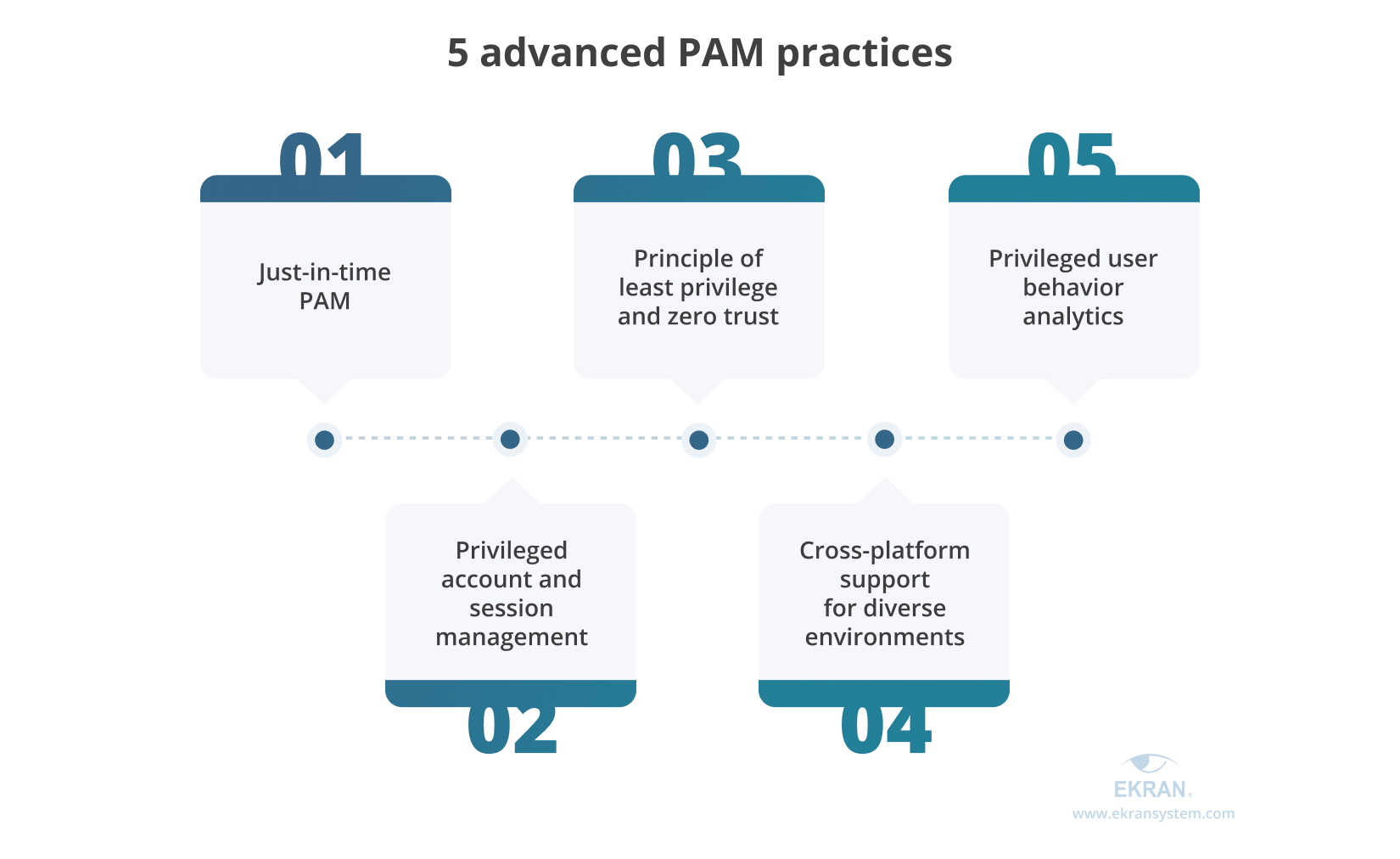
1. Just-in-time PAM
The just in time privileged access management (JIT PAM) approach is designed to ensure that a privileged user has a valid reason to access a sensitive resource and can access it only for a limited time. This way, a user is provided with enough time to work with the resource without getting permanent access to it.
Implementing JIT PAM helps organizations reduce the following risks:
- Security incidents caused by account theft
- Privilege abuse and misuse
- Excessive standing access privileges
To adopt the JIT PAM approach, your organization needs to develop a policy that describes which users under which conditions can access which resources, as well as mechanisms to request, provide, and revoke access to these resources. You’ll also need software to provision and manage temporary privileged access.
As an all-in-one insider risk management platform, Ekran System provides you with several tools to implement JIT PAM:
- One-time passwords, which you can provide to users that rarely require access to a resource
- Time-based user access, allowing privileged access to sensitive data for a limited time
- Manual access request approval to make users send a request to an IT administrator and explain why they need access to sensitive resources. Based on this explanation, the administrator decides whether to approve or deny access.
- Integration with ticketing systems to provide users with access based on written requests and proven needs to work with sensitive resources
Why Do You Need a Just-in-Time PAM Approach?
2. The principle of least privilege and zero trust
What is the principle of least privilege? In brief, the principle of least privilege is designed to limit user access rights only to resources users need. The zero trust approach adds mandatory user and device authentication before allowing access to critical assets. Both practices can help you:
- Granularly configure user access privileges based on needs
- Protect sensitive data from unauthorized and excessive access
- Reduce the possibility of cybersecurity threats from inside and outside
You can adopt both principles using the following Ekran System capabilities:
- Granular access management system to configure access rights for user groups and individual users, review rights quickly, and implement a role-based access control model
- Multi-factor authentication to verify the identity of a privileged user
When implementing zero trust principles to your security system, you can also use one-time passwords, time-based access, and manual access request approval.
3. Privileged user behavior analytics
Each user leaves a digital trail of unique characteristics when they interact with data. The trail includes usual login and logout times, average activities during the day, typing rhythm, typical mouse movements, etc. Software based on machine learning and artificial intelligence algorithms can analyze the specifics of user behavior, create a baseline profile, and alert you on any actions that deviate from the norm.
For example, each user connects to the corporate network at a certain time that’s convenient for them. Say that a user always logs in around 9 AM. In this case, it will be weird if they try to connect at 10 PM. Ekran System’s UEBA can detect and alert you to such unusual events, providing you with the possibility to investigate and prevent a potential security incident.
User behavior analytics is especially efficient at detecting account hacking and theft. If a hacker obtains credentials to a privileged account, rule-based security systems wouldn’t consider their access attempts suspicious because this account has elevated privileges. Yet user behavior analytics can recognize unusual actions and alert IT administrators of a possible security violation.
7 Best Practices for Building a Baseline of User Behavior in Organizations
4. Privileged account and session management
Privileged account and session management (PASM) is one of the key PAM elements according to the Buyers’ Guide for Privileged Access Management by Gartner (subscription required). PASM is focused on the protection of privileged accounts, as well as monitoring and managing their sessions.
In particular, with PASM, you’ll be able to securely grant, revoke, and rotate privileged user credentials as well as record and review user sessions. This way, you can prevent or quickly detect cases of account theft and malicious insider activity.
Ekran System helps you achieve this goal by providing all required privileged user management functionalities:
- User activity monitoring. Privileged user monitoring helps you monitor, record, and review user sessions with any level of privileges. Our platform captures all screen activity and lots of metadata on user actions, and it encrypts records to protect them from theft. Your administrators can review user sessions in real time and in records using a built-in video player.
- Password management. This feature helps you automate and secure any activity with privileged credentials. It creates and stores strong credentials, provides them to users when necessary, and revokes them after a set period of time. Ekran System also encrypts all credentials, making password leaks and theft almost impossible.
Privileged Account and Session Management: How To Deploy It
5. Cross-platform support for diverse environments
The IT environment of a modern enterprise consists of endpoints that use multiple platforms, on-premises and cloud services, and real and virtual machines. Protecting privileged access across all corporate instances can be a challenge since most cybersecurity solutions support only a limited range of platforms.
Ekran System can help you tackle this challenge since our platform can secure endpoints on Windows, Linux, macOS, Citrix, and virtual desktops. You can deploy Ekran System software in your AWS and Microsoft Azure environments. Also, you can easily reassign already purchased Ekran System licenses between your endpoints instead of requesting a new license every time you create a new virtual machine.
Conclusion
With the variety of solutions on the PAM market, it may be challenging to choose software that fits your organization’s needs in terms of cybersecurity and compliance with IT laws, standards, and regulations. Lots of tools are marketed as must-haves, when in fact only certain types of organizations need them. This situation puts organizations at risk of bloating cybersecurity budgets and complicating infrastructure with unneeded security solutions.
Ekran System provides a robust and diverse PAM toolset that helps organizations get privileged access under control, manage it securely and efficiently, and comply with cybersecurity requirements. With two Ekran System editions and pricing based on the number of purchased licenses, you can choose and pay for the range of capabilities your organization needs.
Request a free Ekran System demo to see how our platform can help you improve and streamline privileged access management activities in your organization!





