The world is changing rapidly, with organizations facing new cybersecurity challenges all the time, forcing them to continuously update their cybersecurity strategies. This is especially relevant when it comes to events that have a global effect, like the COVID-19 pandemic and Russia’s invasion of Ukraine.
To assist organizations in keeping their critical assets safe, we’ve compiled a set of key recommendations on how to protect key data and systems from the different types of cybersecurity threats. This article will be helpful to you in building a comprehensive and robust cybersecurity strategy.
How global events are affecting global cybersecurity
It’s crucial to learn from events that may affect the global state of cybersecurity. The COVID-19 pandemic forced many organizations to think about how to develop a cybersecurity strategy due to employees working remotely. Russia’s invasion of Ukraine, in turn, has once again shown that organizations need to pay close attention to sources of both outsider and insider threats.
Russian hackers targeted various Ukrainian systems even before the invasion began, aiming to compromise their networks and operations by way of malware and DDoS attacks. And the better your organization is prepared to handle such attacks, the higher the chances of maintaining the normal operation of your business processes.
In addition to this, hundreds of international companies have suspended their operations in Russia, from McDonald’s to Starbucks, and from Apple to Microsoft. In such companies, employees who have strong political and ideological persuasions, or just disagree with the organization’s public position on the war, might turn into malicious insiders. This could result in increasing state-sponsored espionage, intellectual property theft, sabotage, and other insider-related cybersecurity incidents.


This might be particularly concerning for companies who are considering leaving the Russian market or expressing support for Ukraine.
Fortunately, a set of best practices exists that organizations can follow to improve the sustainability of their cybersecurity defenses, and to enhance the protection of their critical data and processes. Below, we describe some of these practices and possible ways to implement them when developing a cybersecurity strategy.
5 Industries Most at Risk of Data Breaches
Let’s discuss the following eight cybersecurity measures that all companies can implement to build a cybersecurity strategy for their business, so as to protect themselves in the ever-evolving cybersecurity landscape.
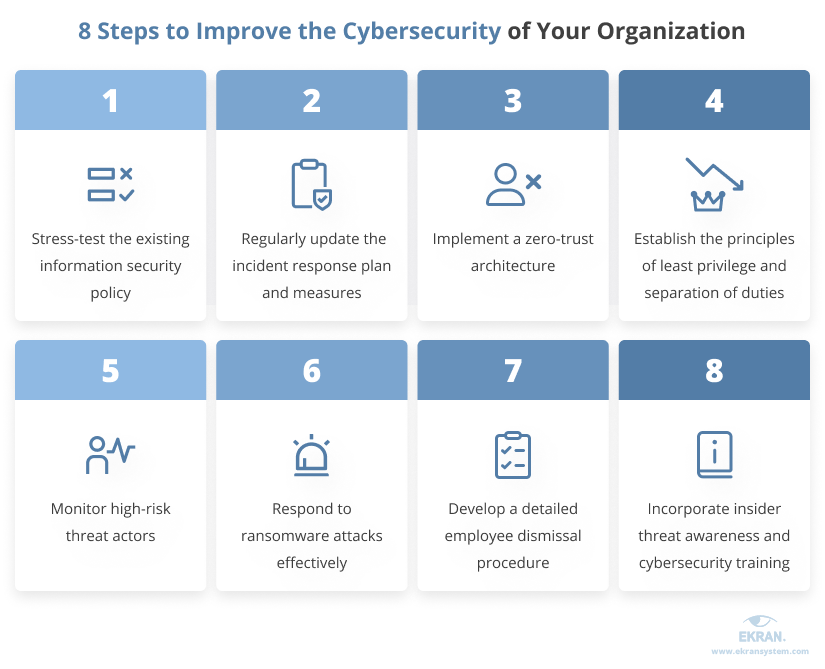
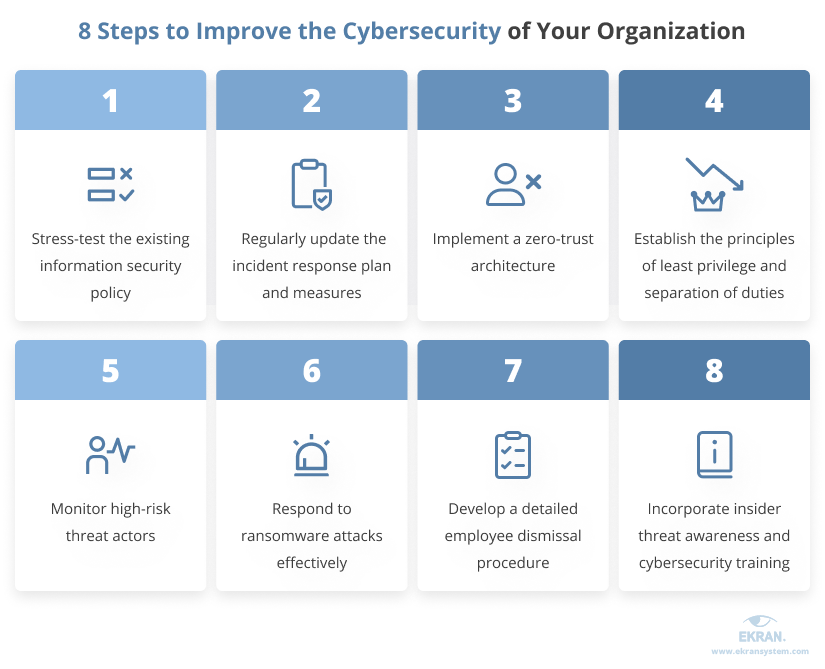
Let’s take a closer look at each of these measures below:
1. Stress-test the company’s existing information security policy
Discover your cybersecurity weaknesses.
Although most companies have an information security policy in place, only a few have effectively tested it. Yet only by running comprehensive and systematic tests on your information protection procedures and mechanisms can you understand how rapidly, effectively, and precisely you can respond to arising cyber threats.
Therefore, consider stress testing your information security policy by simulating different attacks or cybersecurity incidents, and assessing your organization’s readiness to respond to them. The results will assist you in evaluating the cybersecurity measures and technologies you already use, and identifying what updated practices you need to implement to enhance your organization’s response to various cybersecurity incidents. Also, you may look through effective IT security policy examples to establish new procedures within your organization.
2. Regularly update your company’s incident response plan and measures
Get ready for new cyber challenges.
An incident response plan (IRP) is a document containing instructions for responding to security incidents, such as a data breach or a ransomware attack. If a company isn’t routinely updating its incident response plan, they’re putting themselves at risk of cyber attacks.
Start updating your IRP by evaluating an inventory of your critical assets, and considering whether the current business environment warrants any changes to it. Regularly revise the list of the employees and authorities that should be contacted in case of a particular incident, to ensure that your employees know who to reach out to first. Consider how changes in the external and internal threat environments could influence the company’s cybersecurity, and whether you have sufficient response measures in place to meet new security risks.
Security Incident Investigation
3. Implement a zero-trust architecture
Trust no-one, verify everyone.
Implementing a zero-trust architecture can significantly reduce cybersecurity risks from both inside and outside the company’s infrastructure. The creator of this approach, John Kindervag, states that companies must not automatically trust anything, either within or outside their perimeters. Instead, businesses need to verify everything that attempts to connect to their systems before granting access.
Therefore, steps you can take to implement zero trust in your organization, and thus secure your critical assets from core cyber threats include:
- Remove all default access permissions
- Verify user identities with measures like forced multi-factor authentication
- Always validate devices that you grant access to your network to
In addition to these, access should only be granted to the extent required to perform a particular task.
4. Implement the principles of least privilege and separation of duties
Minimize the scope of attacks.
Least privilege is when a company only provides its staff with the account privileges they require to do their jobs. The principle of least privilege can also be enhanced by using separation of duties to minimize the risks of your insiders committing malicious actions. Here are a few ways in which organizations can implement these two principles:
- Set up role-based access controls to prevent members of staff from accessing data or services that their work does not require.
- Make sure that personnel in administrative roles have separate, distinct accounts for their managerial and non-managerial tasks.
- Require authorization from two or more users for copying information to removable storage devices, and consider encrypting the data.
- Require two or more system administrators to authorize the deletion of critical data and the changing of setup configurations.
Why Do You Need a Just-in-Time PAM Approach?
5. Monitor high-risk threat actors
Keep an eye on suspicious insiders.
High-risk actors are those insiders whose actions can potentially lead to cybersecurity incidents. Monitoring high-risk threat actors can allow you to prevent a security incident before it happens.
If you know the specific methods that malicious insiders use, you can take preventative measures to secure your critical assets against potential threats. Also, consider involving non-cybersecurity professionals in the process of identifying employees who are high risk in terms of becoming a threat actor. Say, in cases like the war in Ukraine, you might need the assistance of HR specialists to assess such risk factors as the political preferences of your employees.
Companies need to monitor their security systems and high-risk employees to react to suspicious or potentially malicious behavior in near real-time. Implementing user and entity behavior analytics (UEBA) technologies makes spotting these high-risk actors much more effective.
6. Respond to ransomware attacks effectively
Secure your most critical data.
The statistics on ransomware attacks are staggering. The Cybersecurity and Infrastructure Security Agency revealed that in February 2022, 14 of the 16 U.S. critical infrastructure sectors were targeted by ransomware attacks. Your security team should have a reliable information security strategy that includes robust technical controls and regular employee training to mitigate incidents, as well as clear procedures to respond to them.
The response strategy must document which security tools are used for ransomware protection, mitigation, and recovery capabilities. It is crucial to regularly evaluate and test this cybersecurity strategy for your enterprise (annually, quarterly, and monthly) to guarantee that system recovery from backups can be done quickly and reliably in the event of a ransomware attack.
15 Cybersecurity Best Practices to Prevent Cyber Attacks in 2022
7. Develop a clear and detailed employee dismissal procedure
Mitigate risks from your departing employees.
Employees may compromise your organization’s cybersecurity if they are unhappy, for example, due to dismissal or staff layoffs. Security risks are especially high when you are considering terminating the contracts of a large number of employees. You, therefore, need to consider adding such employees to a high-risk group, in order to monitor them accordingly before they leave the company.
On the company terminating an employee’s contract, it is essential to take the following steps:
- Recuperate all company equipment and software licenses from the employee
- Restrict the employee’s access to corporate accounts, networks, and groups
- Revoke the employee’s passwords
7 Best Practices to Prevent Data Theft by Departing Employees
8. Incorporate insider threat awareness and cybersecurity training
Turn your employees into your cyber shield.
While employees can be an enterprise’s greatest threat, they are also the first line of defense. Conduct employee training on existing and newly arising cybersecurity risks to help your employees prevent attacks from happening. This is particularly important to enable your employees to better identify phishing emails, which can often dodge email filtering solutions.
In addition to this, insider threat awareness training is critical to keeping your organization’s sensitive data out of the wrong hands. It is vital to adequately educate staff about the cybersecurity risks relevant to your organization and the indicators of an insider threat so that your employees can identify and report cybersecurity incidents when they emerge. Inform employees about who they should contact first if they suspect an insider threat.
How Can MITRE ATT&CK Help You Mitigate Cyber Attacks?
How to improve your cybersecurity response capabilities with Ekran System
Ekran System is a comprehensive insider risk management platform that can strengthen a company’s cybersecurity strategy at a number of different levels including managing user identities, managing access of privileged users, monitoring user activities, and detecting and responding to cybersecurity incidents in near real-time. It is a comprehensive cybersecurity solution that companies can use to detect malicious insider activity, automate their response to cybersecurity incidents, and provide evidence for investigation.
Here are a few of the features that Ekran System provides:
- Employee and third-party monitoring
- Recording all user sessions, including video and metadata
- Analyzing user behavior to detect abnormal activity
- Enhancing incident response with custom alert rules
- Blocking users, specific devices, and device types
- Generating reports in protected formats for forensic investigation
Conclusion
Events that affect the daily lives of millions of people, such as the war in Ukraine, inevitably also affect the state of global cybersecurity. In today’s fast-changing environment, organizations must be ready to respond to such unexpected events in an effective manner.
In particular, it is essential to regularly assess and prioritize risks to enhance your cybersecurity strategy and implementation plan, and take appropriate measures to secure your most valuable assets in case of a security incident.
Using Ekran System, you can mitigate the risks of state-sponsored espionage and other insider threats, as well as timely detect compromised employee accounts.
Enhance your organization’s cybersecurity now by requesting a FREE 30-day trial version of Ekran System!





