Citrix Session Monitoring and Recording Solution
Monitor insider activity. Detect anomalies. Respond to incidents. ALL-IN-ONE
With its flexible clients, Ekran System provides effective solutions for tracking Citrix user activity. In addition to Citrix session recording, Ekran System delivers a comprehensive set of identity and access management features, real-time alerting, and incident response tool sets.
As a universal insider threat management platform, Ekran System supports virtual environments alongside physical ones, providing powerful solutions for employee monitoring and third-party security monitoring, as well as compliance with multiple security standards.

Citrix monitoring tool screenshots
Citrix monitoring software functionality overview
Overview of functionality
| Citrix XenDesktop | Citrix XenApp | |
|---|---|---|
| Installation | One client per virtual desktop via an automated license pool | One client per published app server |
| Session details | Hostname, username | Full details on remote IP address, hostname, username |
| Session recording | Video of user’s screen accompanied by activity details, including keystrokes and connected devices | Video of user’s screen accompanied by relevant activity details, including keystrokes |
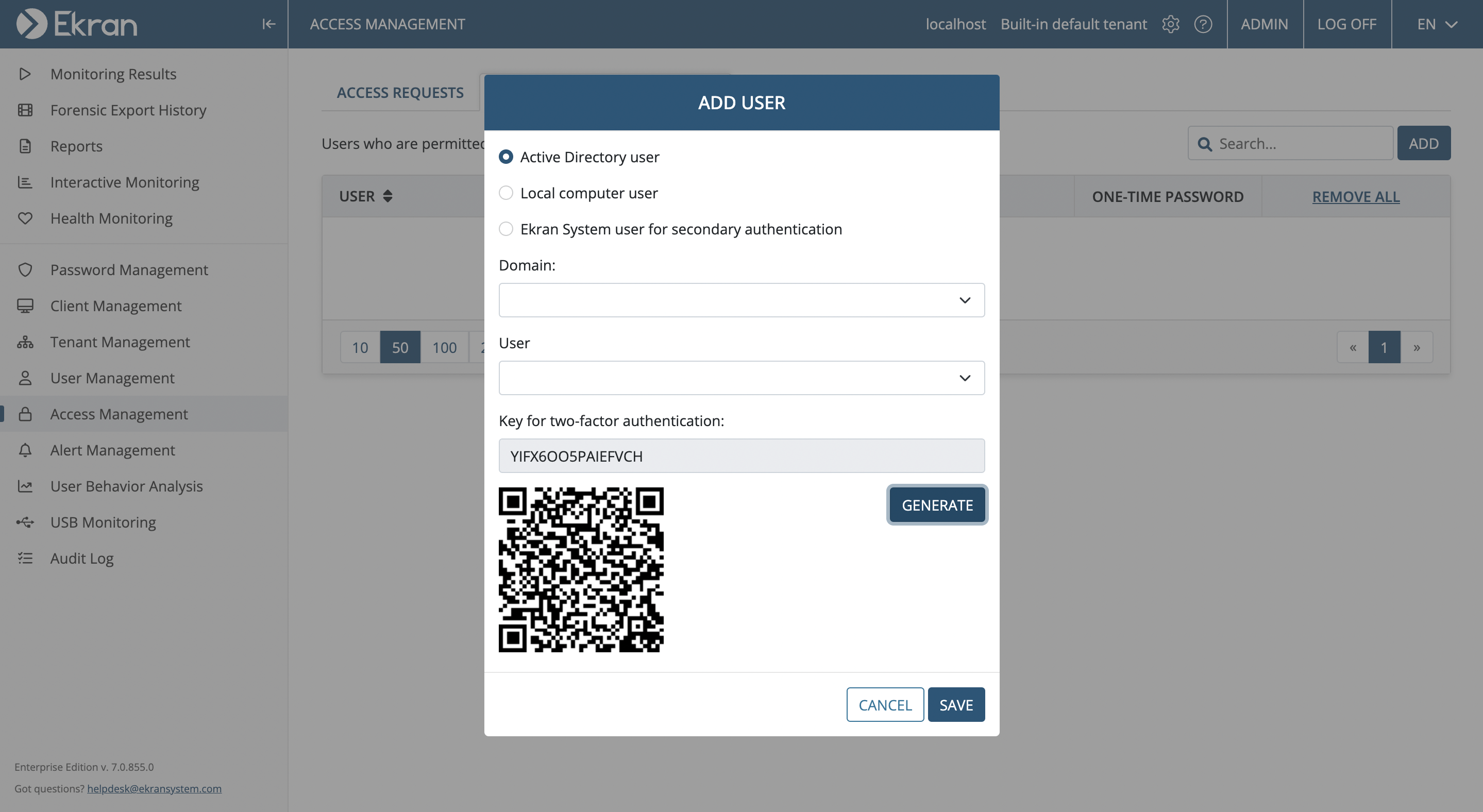
| Identity verification | Two-factor authentication Secondary authentication for shared logins | Two-factor authentication Secondary authentication for shared logins |
| Access management | PASM One-time passwords Access request and approval workflow Ticketing system integration | |
| Alerts and notifications | Predefined templates and customizable rules around activity details | Predefined templates and customizable rules around relevant activity parameters Session initiation |
| Incident response | Live session view User blocking Session termination Warning messages | Live session view User blocking Session termination Warning messages |
Citrix XenDesktop monitoring and control
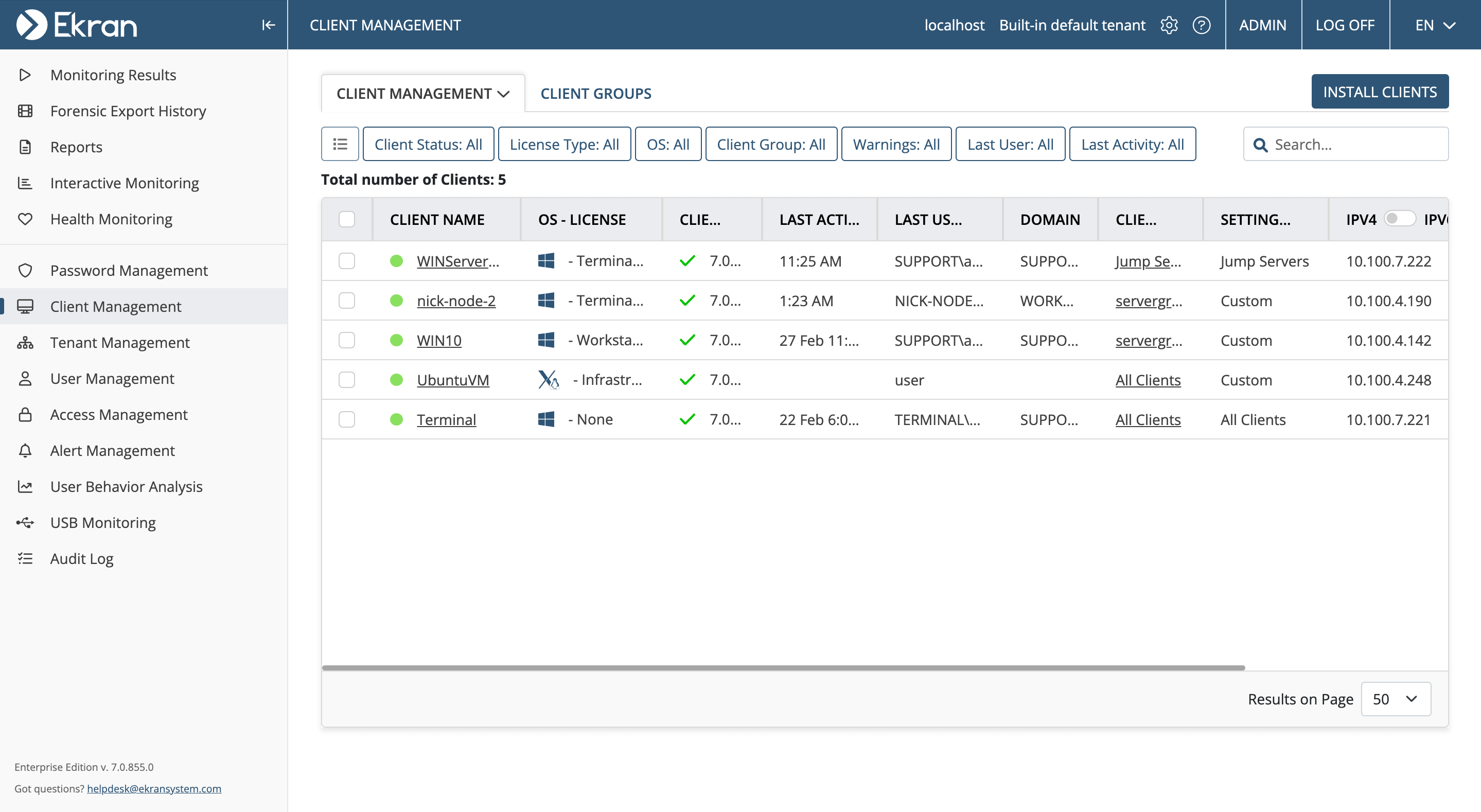
Ekran System workstation clients can be installed on any live Citrix XenDesktop and included in system images to be preinstalled on any new virtual desktop.
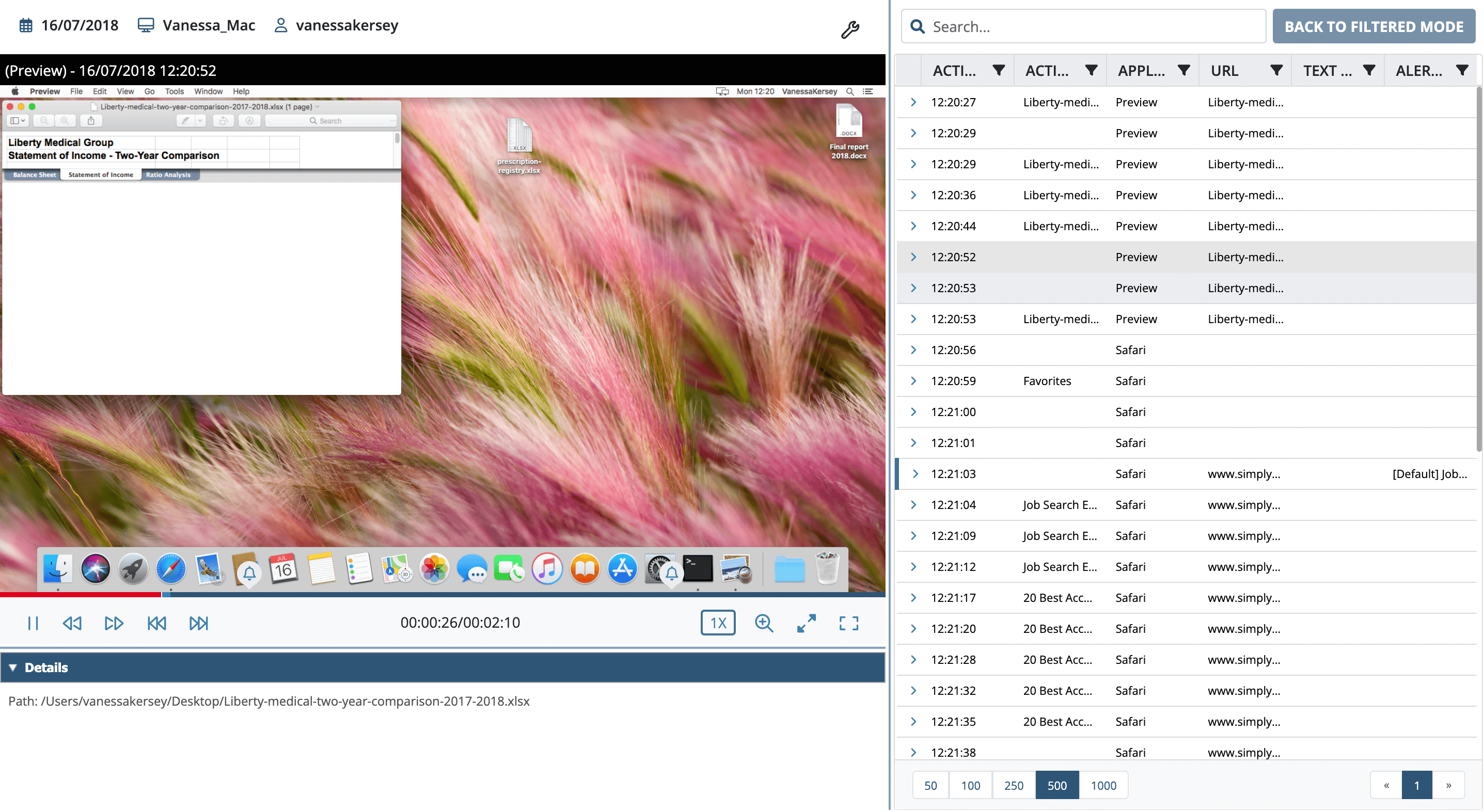
The Ekran client allows you to verify user identity with tools for two-factor authentication and secondary authentication for shared logins. Once a session is allowed, the software records all user activity in a smart screen video format indexed with multilayer metadata:
- Names of active applications
- Opened URLs
- Keystrokes
- Connected USB devices (virtual and physical)
- and other details
When auditing or investigating an incident, you’ll have access to in-session and cross-session search options, fast-forward replay, and various standard and customizable reports to flag potential incidents.
To help you respond to incidents in a timely fashion, Ekran System Citrix employee monitoring software provides a broad set of alert templates along with the possibility to customize them and build your own rules.
When a user performs an abnormal or security-critical action, your team will be notified and provided with incident context so they can check what’s going on and respond immediately. For the most critical cases, alerts can be augmented with automated incident response actions, such as blocking the user, killing the application, and/or displaying a warning message.
Citrix XenApp monitoring and control
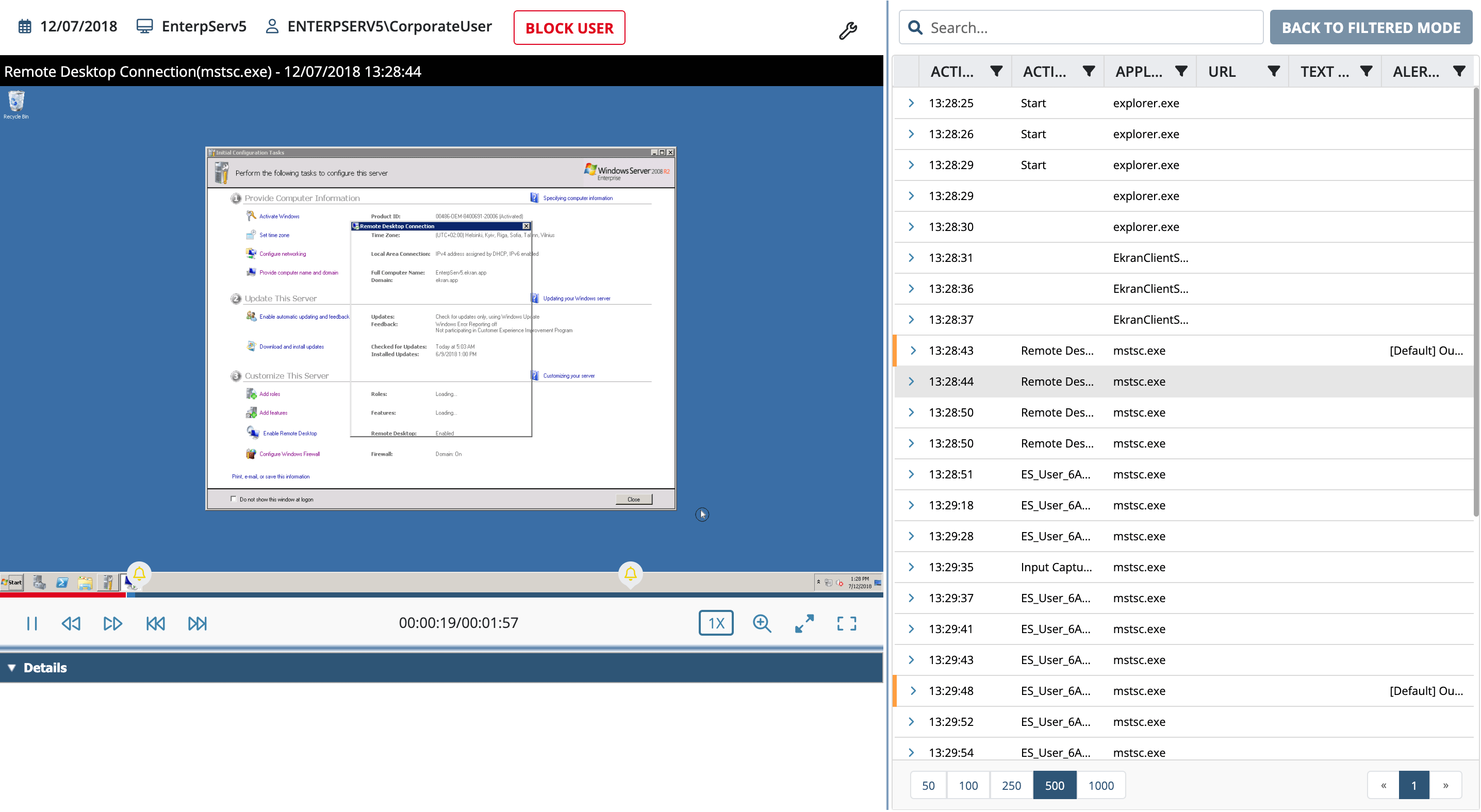
Ekran System is a well-thought-out solution for Citrix XenApp monitoring. For Citrix server monitoring, its Terminal Server client can be installed directly on a published application server, simultaneously recording all concurrent sessions and providing real-time incident detection and response.
The client can be used for Citrix XenApp session recording selectively, only recording for a range of users or host IP addresses or only recording those sessions outside of a white list. Each session recording includes a video recording of the user’s screen (showing all or only selected activities) indexed with details on activities, such as keystrokes or active window title.
Ekran System’s complex alerting system works not only for virtual desktops but for Citrix XenApp sessions as well. Besides alerting about potentially dangerous actions within a session, the system can notify your security team when a session is being established by specific users or from specific IPs. Critical alerts can trigger automated incident response actions such as terminating a session or blocking a user.
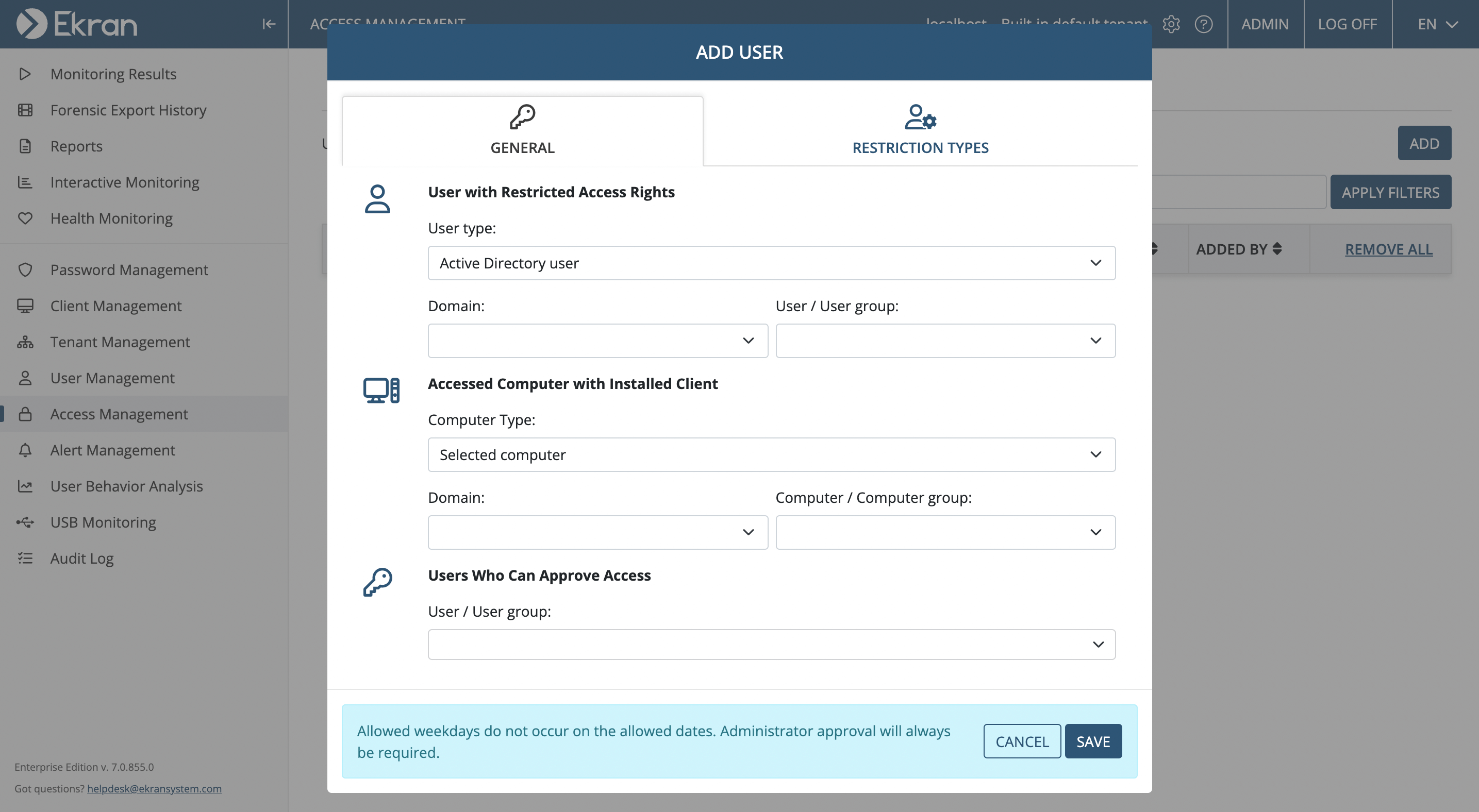
In addition to session monitoring for Citrix , Ekran System provides powerful access management capabilities for Citrix XenApp published application servers. You can choose from a fully-functional privileged account and session management (PASM) tool set for granting temporary access, one-time passwords for emergency access, and access request workflow for even more control. Additionally, you can integrate your access management scheme with a ticketing system. You can verify user identity with Ekran System using two-factor authentication.
In addition to Citrix environments, Ekran System also supports VMware and physical infrastructures in any hybrid scheme. Watch the video to learn more.
Ekran System Citrix monitoring solution benefits
As a powerful Citrix monitoring tool, Ekran System delivers a unique blend of detailed activity monitoring and auditing, access management, and identity management with its monolithic multi-functional endpoint-based agents empowering your Citrix security program.
More Ekran System benefits
Full desktop and server OS support
Supports a wide range of operating systems and any type of network architecture due to its flexible deployment scheme.
Comprehensive activity control
Delivers detailed multi-level Citrix user activity monitoring with strong access control and critical identity management features.
Low total cost of ownership
Simple and straightforward licensing adapts to your needs and deployment size. Ekran System includes floating endpoint licensing and a license pool with automated license provisioning/revoking.
Enterprise friendly
Includes enterprise-ready features such as multi-tenant deployment, high availability, advanced archiving, SIEM and ticketing system integration, and 24/7 support.
Let’s get the conversation started
Contact our team to learn how our insider risk management software can safeguard your organization’s data from any risks caused by human factors. Book a call with us at a time that suits you best, and let’s explore how we can help you achieve your security goals.