VDI User Activity Monitoring Software for VMWare Horizon, Hyper-V, Citrix
Monitor insider activity. Detect anomalies. Respond to incidents. ALL-IN-ONE
Working with a virtual desktop infrastructure (VDI) instead of physical endpoints provides companies with countless benefits. VDI desktops can be created and shut down in a few minutes, can easily be scaled up and down, and cost money only when in use.
But ensuring continuous monitoring of user activity in VDI is challenging: you need to monitor all platforms in your infrastructure and get licenses for all virtual endpoints.
Ekran System is an insider threat management platform that you can use as a virtual desktop monitoring tool and user session recording tool in various environments, including:
- VMware Horizon
- Microsoft Hyper-V
- Citrix
- Amazon WorkSpaces
- Windows Virtual Desktops

Screenshots
Supported VDI platforms
Ekran System can monitor user activity on many VDI platforms, including on popular private clouds and Desktop-as-a-Service (DaaS) solutions.
Private cloud solutions
We are proud to be the official partner of VMware. Ensure employee monitoring in VMware Horizon and VDI user session recording on desktops and apps deployed on-premises or in the cloud, including in hybrid and multi-cloud infrastructures.
Add Ekran System Client to your Microsoft Hyper-V master image to monitor and record any session that connects to a monitored server.
Deploy Ekran System agents to monitor virtual desktops with Citrix XenDesktop installations, or install a Terminal Server client to control Citrix XenApp applications.
DaaS solutions
As an official Microsoft Windows Virtual Desktop value-add partner, Ekran System easily integrates into your Microsoft Azure infrastructure.
Install Ekran System Client on live desktops or add it to VDI master images to monitor and record sessions on Windows Virtual Desktops.
Monitor and record user activity both on Windows-based Amazon WorkSpaces desktops and Amazon Linux 2.
Control activity on Windows Server 2008 R2 and Windows Server 2016 machines that power your AWS infrastructure.
This wide-ranging list of monitored virtual platforms in addition to support for physical Windows and Linux endpoints allows you to monitor user activity across your entire infrastructure with one VDI monitoring solution.
Ensure VDI monitoring with floating licenses
Ekran System uses a floating endpoint licensing approach to allow you to redistribute licenses between endpoints in a matter of minutes.
The best thing is that you only need enough Ekran System Workstation licenses to cover the number of active desktops at a given moment. Ekran automatically distributes floating licenses between dynamically changing virtual desktops. This makes the cost of VDI user monitoring transparent, and the process itself easily manageable.
To automate license provisioning, add Ekran System Client to your virtual machine master image. After that, new desktops will be created with Ekran System Client already installed on them. When a virtual desktop is launched, the client will automatically get a license from the general pool and start monitoring activity on the new endpoint. When an administrator shuts down the endpoint, the license is released and returns to the pool.
Watch our demo video to learn how to monitor virtual servers and desktops with Ekran System.
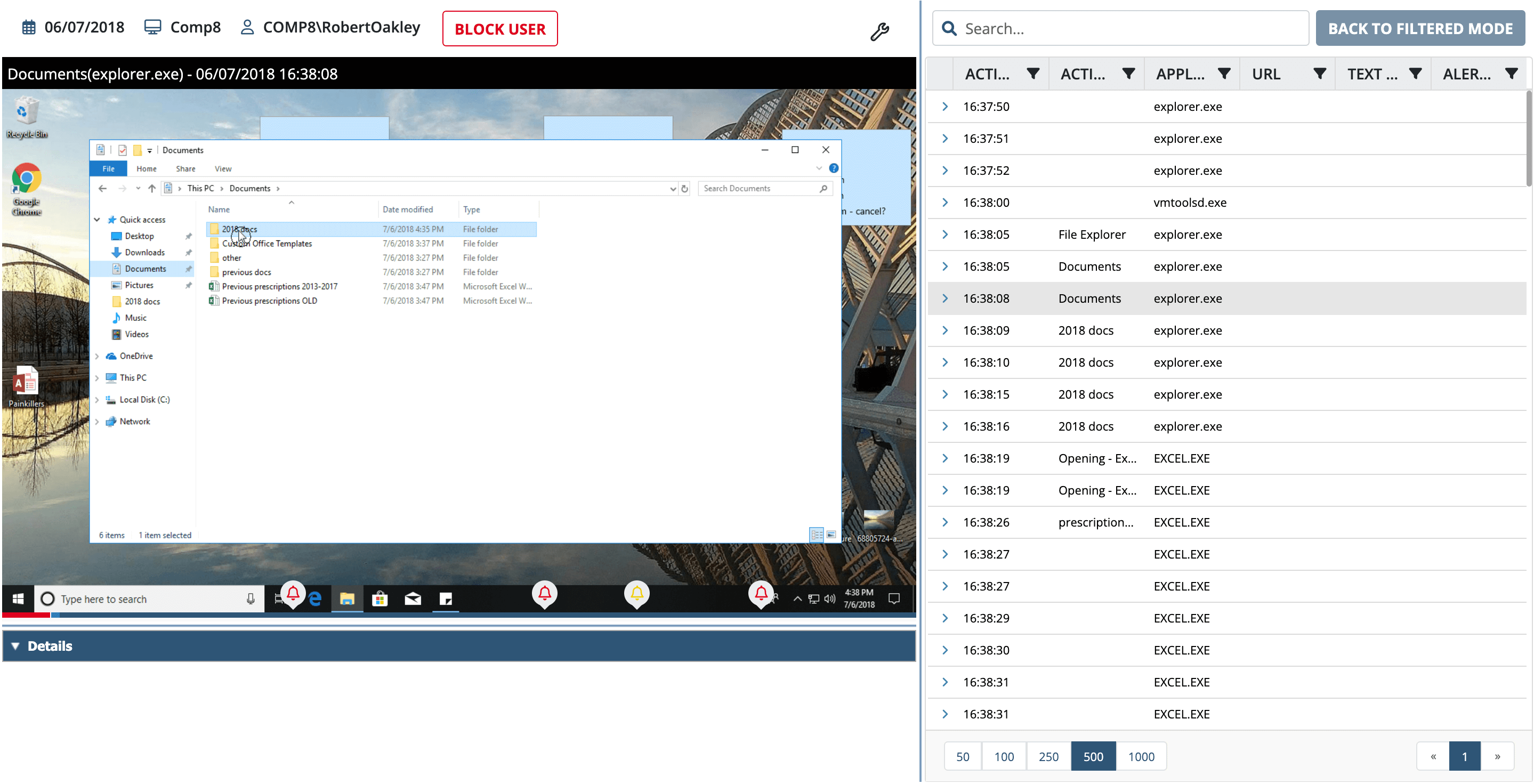
Ekran System remote computer monitoring software will record any RDP session, Telnet, console, or remote PC management session as a video and audio stream together with all typed keystrokes and other metadata.
Watch our demo video to learn how to monitor virtual servers and desktops with Ekran System.
Additional benefits of Ekran System
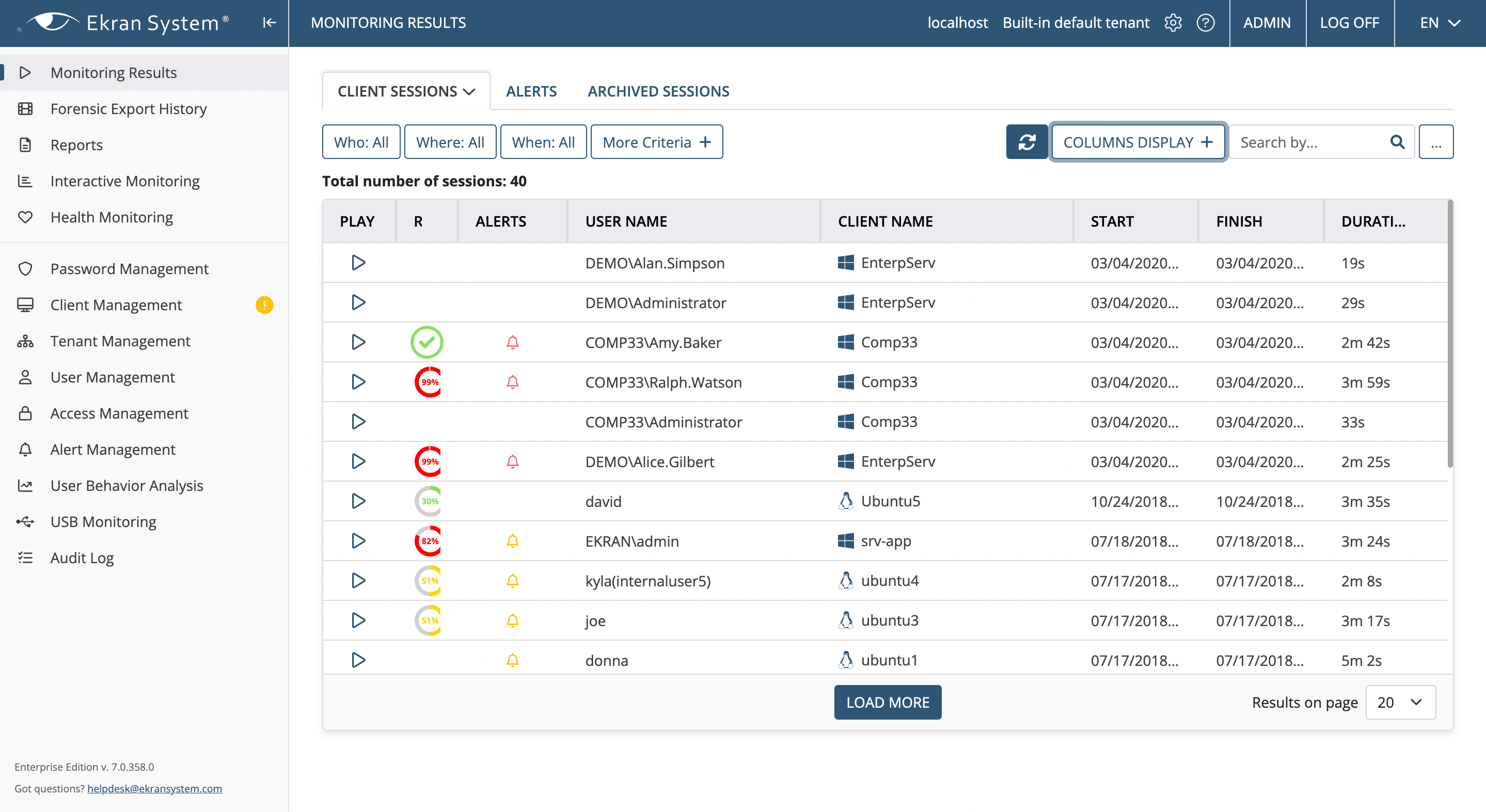
Ekran System is an all-in-one insider threat management platform that effectively deters, detects, and disrupts insider threats. VDI monitoring software by Ekran System provides you with multiple benefits:
Virtualization-ready agents
The Ekran System Client can be included in a virtual machine master image to automatically monitor the user activity of any newly added virtual desktop.
Easy deployment
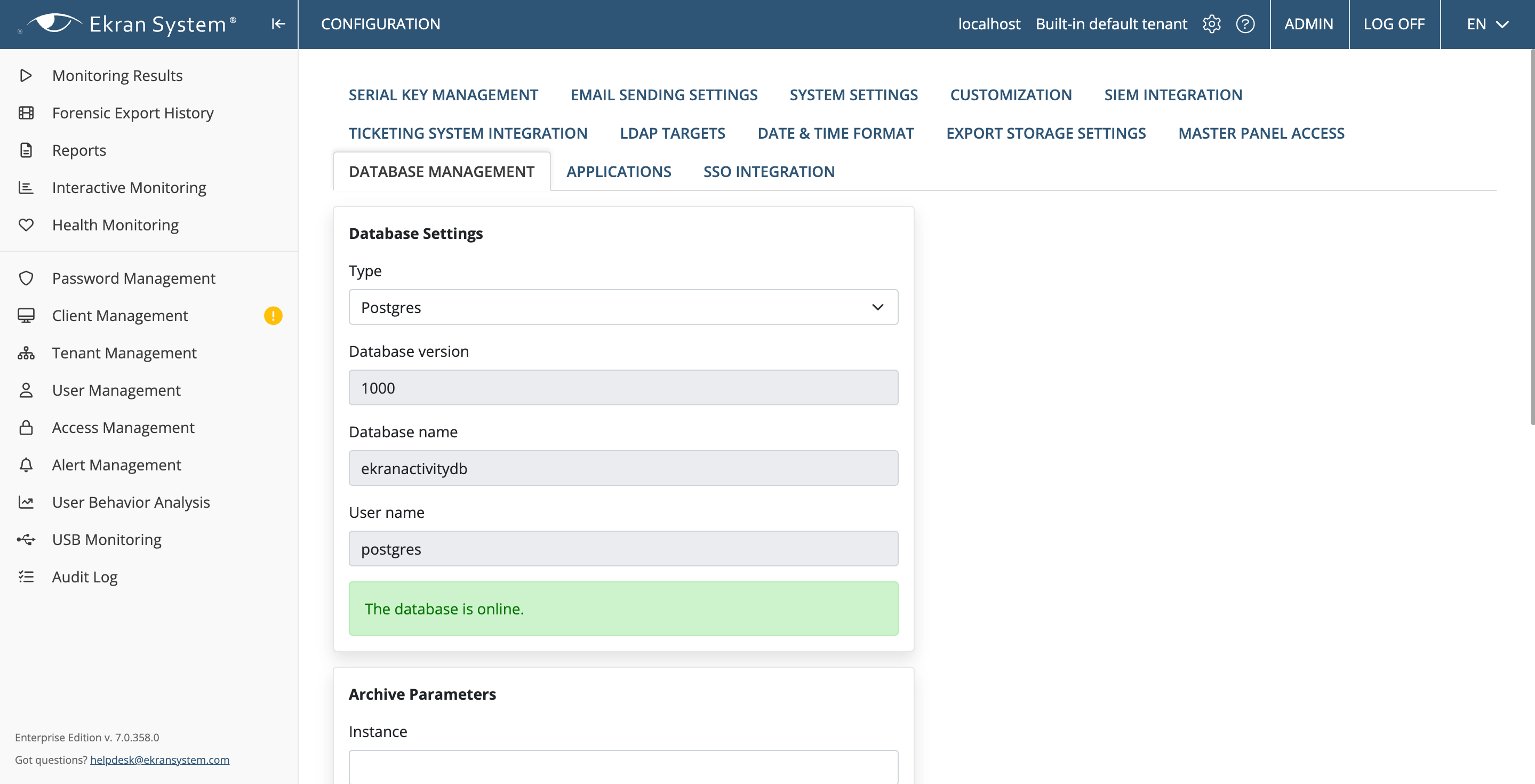
Ekran System doesn’t require any additional configuration changes on your servers. Deploying and configuring the client takes less than 20 minutes. After that, you can start using VDI monitoring tools to control your virtual endpoints.
Context-rich recordings
Ekran System captures data on visited URLs, active window titles, typed keystrokes, USB device connections, and other user actions. All collected data is available in the web-based review and analysis tool.
Fast incident response
When a default or custom rule-based alert is triggered, you’ll get an email notification with details about the cybersecurity event and a link to the suspicious session. You can automatically or manually show a warning message to the user, block the session, or block the user.
Let’s get the conversation started
Contact our team to learn how our insider risk management software can safeguard your organization’s data from any risks caused by human factors. Book a call with us at a time that suits you best, and let’s explore how we can help you achieve your security goals.