USB Device Management Software
Monitor insider activity. Detect anomalies. Respond to incidents. ALL-IN-ONE
USB devices are irreplaceable in modern offices. Yet when poorly managed, they can become the reason for a cybersecurity incident resulting in data and endpoint compromise.
Instead of prohibiting the use of all USB devices, you can granularly control them with USB management software like Ekran System.
Ekran System® delivers continuous monitoring and granular management of USB devices, enabling you to enhance your user activity monitoring and access management efforts. Our platform gives you the power to decide which USB devices to monitor, allowlist, or block depending on their type or even their vendor.

When to use USB device management
Establishing granular, properly configured USB device control and monitoring can help your organization secure critical resources from misuse and compromise. In particular, deploying USB management software enables:
- Secure implementation of a BYOD policy
- A secure shift to remote work
- Establishment of a zero-trust architecture
- Compliance with key data security standards and regulations
Use USB device management when you
Implement a BYOD policy
Build a zero-trust architecture
Work with telecommuters
Need to meet compliance requirements
Ekran System provides you with all capabilities needed to establish strong yet flexible USB device management.
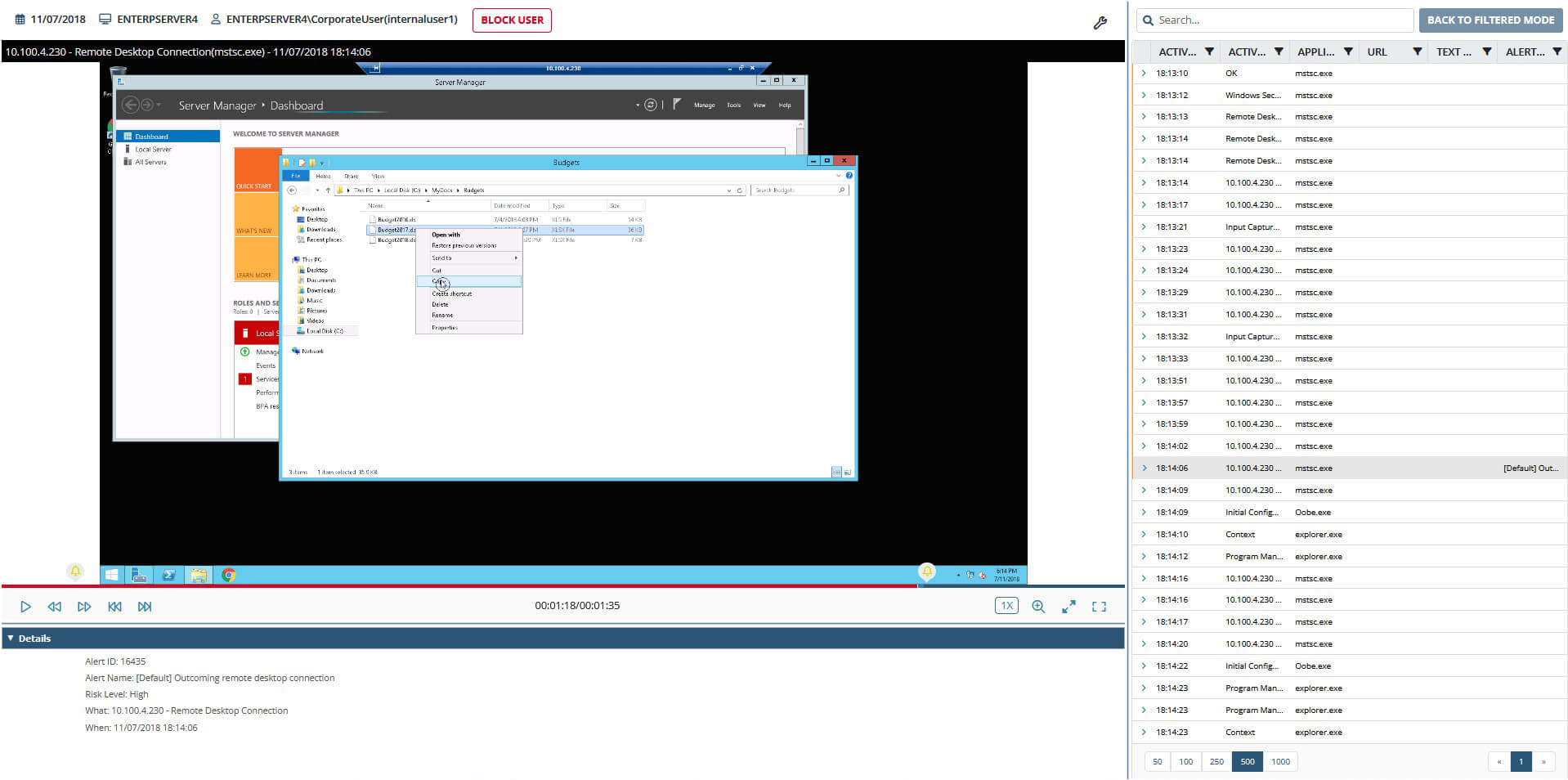
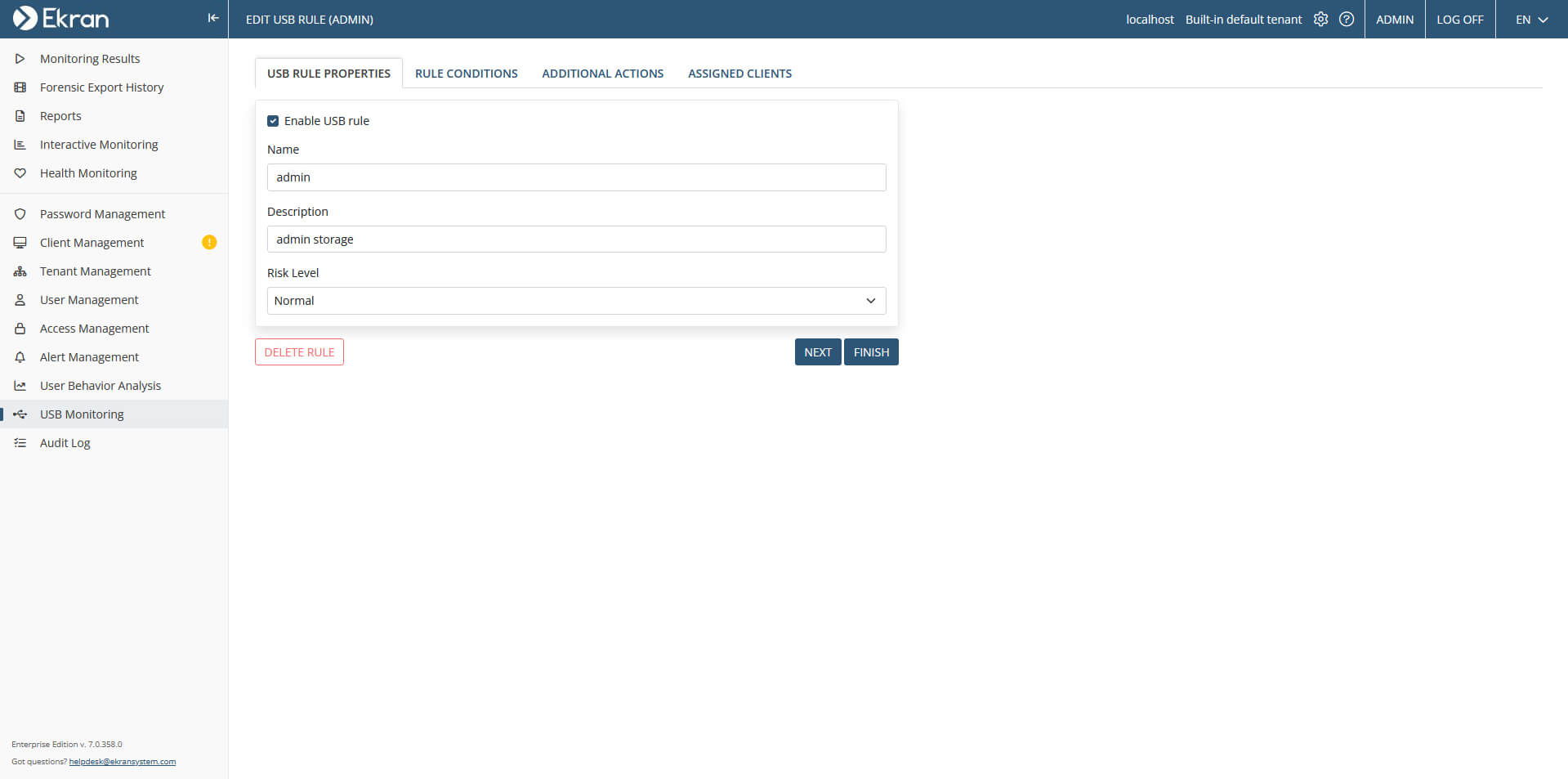
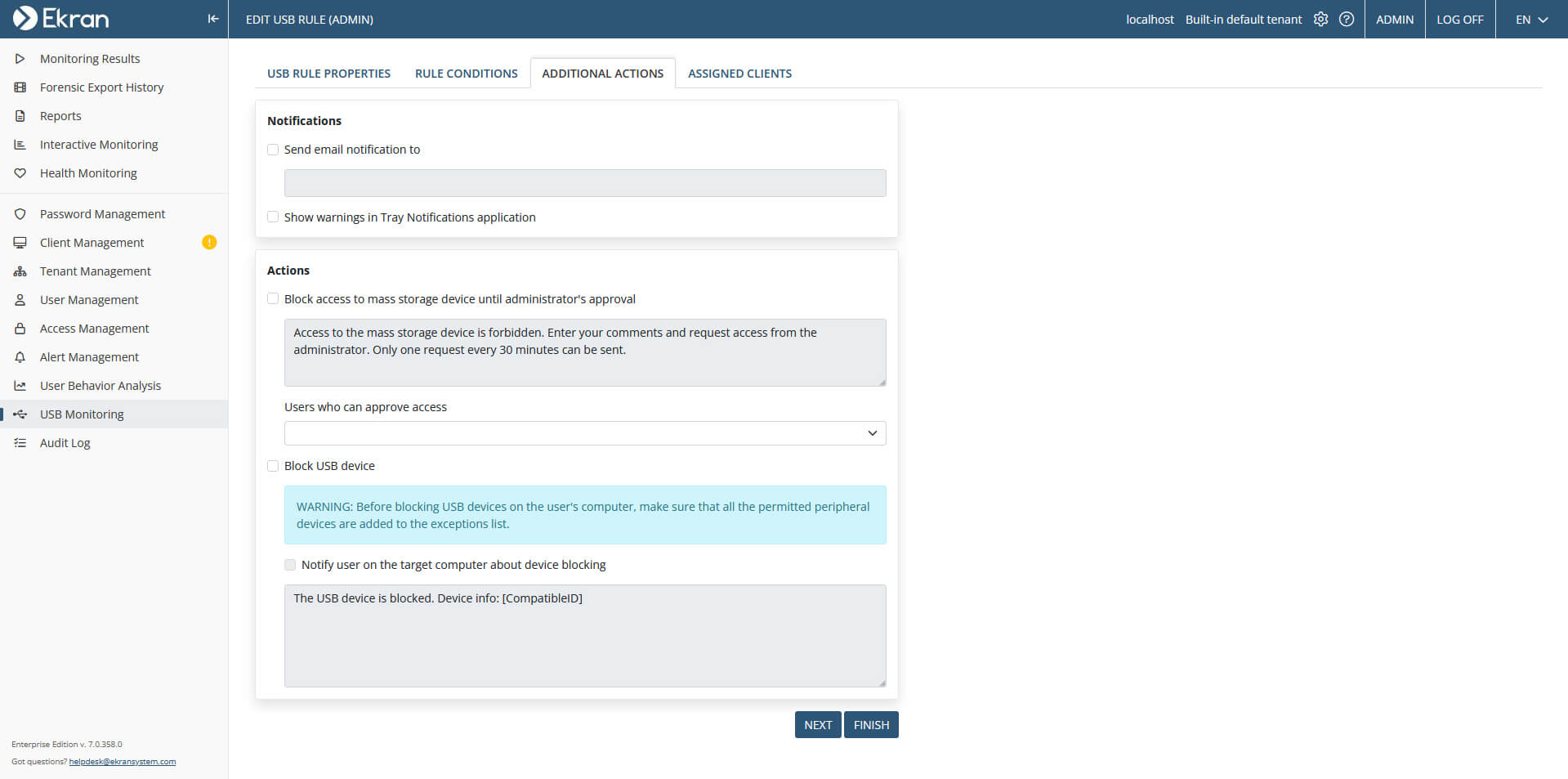
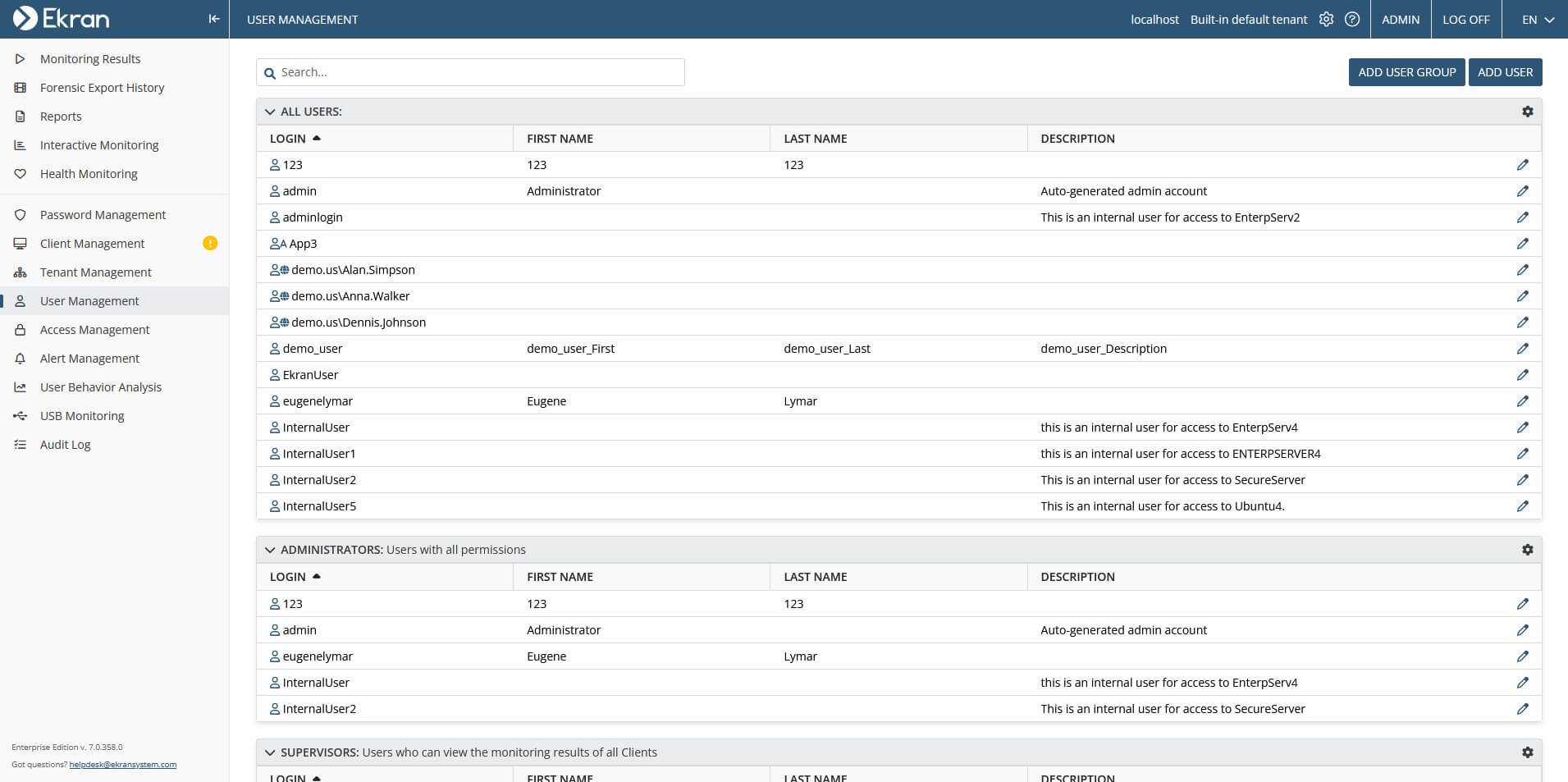
Screenshots of managing USB devices with Ekran System®
How Ekran System’s USB device management works
You can use Ekran System to filter the use of USB devices, both manually and automatically. Our USB device management functionality works on two levels:
- Automatic monitoring
- Kernel-level monitoring
Two levels of Ekran System’s USB device management
Automatic monitoring
Monitors all connected USB devices. No additional configurations
are required.
Kernel-level monitoring
Enables you to set rules for USB activity monitoring, permitting, or prohibiting the use of particular USB devices.
Ekran System allows you to manage USB devices by providing you with all the necessary functionality to:
- Continuously monitor all connected USB devices — Review and analyze Ekran System’s records of all USB device-related events along with other user activity logs on a monitored endpoint.
- Block connected USB devices — Specify which devices to block permanently and which can only be accessed after manual admin approval. Show custom pop-up notifications or an access request form to your employees whenever they try to connect a restricted USB device.
- Whitelist separate USB devices — Create individual exceptions so that Ekran System won’t monitor and block specific devices on chosen endpoints.
- Get notified of suspicious connection attempts — Have your security personnel receive real-time alerts when a user tries to connect a potentially dangerous or restricted USB device. Ekran System can send notifications via email or system tray messages.
Types of USB devices commonly managed by Ekran System
Mass storage devices
Windows portable devices
Wireless connection
devices
Modems and network adapters
Audio devices
Video devices
Human interface devices
Printers
Composite devices
Benefits of Ekran System’s USB device monitoring and management
Secure your critical data and systems against cybersecurity threats by leveraging the key benefits of Ekran System’s USB control software:
- Automatic monitoring — There’s no need for extra configurations, as Ekran System automatically monitors all connected USB devices by default.
- Granular management of USB devices — Create separate USB device-related rules for specific endpoints or groups of endpoints.
- Support for all types of USB devices — Get full visibility and control over any USB device connected to an endpoint protected by Ekran System.
With Ekran System’s rich user activity monitoring capabilities, you can always see what’s going on on a particular endpoint by reviewing a user session in real time. And to further analyze information gathered by the platform, you can form a report on connected and blocked USB devices.
Get more than just USB device monitoring
With Ekran System, you get more than just USB activity monitoring software. Our insider risk management platform enables you to effectively deter, detect, and disrupt insider-related security threats and incidents.
Robust user activity monitoring. Get to see who does what with your sensitive data, critical systems, and servers. Monitor the activity of your employees, both on-site and off-site, as well as third-party contractors.
Detailed session records. Review and analyze the full context of any event. Use Ekran System’s searchable session records to audit your organization’s cybersecurity, assess possible risks, or investigate a security incident.
Fast incident response. Set custom alerts or choose fitting predefined alerts from Ekran System’s library to detect potential cybersecurity threats in a timely manner. Handle security incidents manually or enable automated incident response to block or terminate suspicious users, applications, and processes.
Cybersecurity compliance. Leverage Ekran System’s rich access and identity management capabilities to meet the latest cybersecurity compliance requirements. Secure access to your critical assets with our two-factor authentication, data encryption, and password management functionalities.
Continuous support. Ekran System’s support team is there for you whenever you have a question about using or configuring our platform. You can always learn more about the platform’s specifics in our rich knowledge base or reach out to our support team using the support form.
FAQ
USB blocking is a security measure that limits capabilities of USB ports on user devices. This measure allows you to manage USB devices and restrict their use to protect your computers from malware, data theft, and other malicious activity.
Any organization or individual that needs to protect their sensitive data and systems should consider using USB-blocking software. USB-blocking software is especially vital for organizations in finance, healthcare, manufacturing, education, and the public sector since they store loads of sensitive information.
One way to restrict the use of USB is to deploy USB control software. It allows you to specify which devices are allowed to be connected to computers within your network and which aren’t.
A variety of USB activity monitoring software enables you to monitor USB devices within your network. These platforms can continuously monitor and log USB device connections.
USB control software like Ekran System offers all the necessary tools for comprehensive USB device monitoring. With Ekran System, you can:
- Monitor connected USB devices
- Receive notifications on USB connections
- Block specific USB devices
- Configure a USB device approval workflow
Let’s get the conversation started
Contact our team to learn how our insider risk management software can safeguard your organization’s data from any risks caused by human factors. Book a call with us at a time that suits you best, and let’s explore how we can help you achieve your security goals.