Privileged access rights are the gateway to critical systems and data. Providing users with elevated privileges is a standard practice, as employees sometimes need access to sensitive data to perform their jobs. At the same time, there’s always a risk of privilege misuse with the aim of industrial espionage or cyberattacks.
In this article, we explain why elevated privileges can pose a threat to your organization’s cybersecurity, how privilege escalation works, and what risks are hidden behind uncontrolled privilege escalation. We then offer a list of practices to prevent privilege abuse.
Cybersecurity risks of privilege elevation and escalation
What’s the true danger of elevated privileges?
Every organization strives to provide employees with the access rights they need to perform their jobs efficiently and fast. Depending on their positions and tasks, employees can have regular or privileged permissions for accessing specific assets within the corporate network.
The majority of an organization’s employees are standard users. These employees don’t need access to sensitive corporate data or systems to perform their routine work. Regular users have limited access rights and can’t directly interact with critical data or systems. All they need to do their jobs are computers and various internal business applications.
Privileged users, in turn, are usually empowered with elevated rights for accessing critical data, systems, and applications. Organizations can provide privileged accounts to be shared among certain groups of employees or provide a unique privileged account to each employee with elevated access rights.
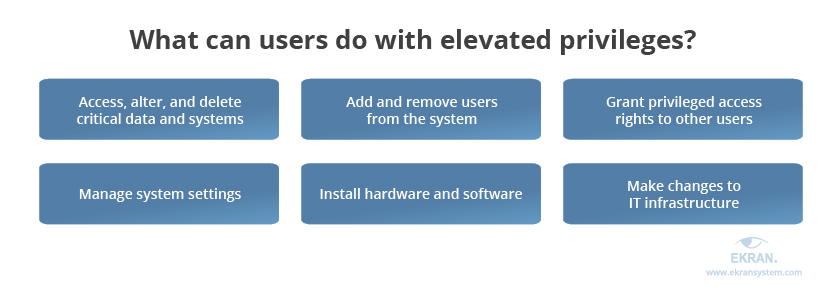
Elevated privileges are most often provided to groups of employees who need additional permissions to perform their day-to-day jobs.
Such users include:
- administrators who install/remove software and change configurations
- IT managers responsible for running web, database, and application servers
- supervisors and managers who work with sensitive information like financial or HR data
- security officers responsible for the organization’s cybersecurity.
However, these privileges have to be wisely assigned and properly managed and secured. Otherwise, they can put the security of your critical data and systems at risk.
There are three common risks associated with elevated user access rights.
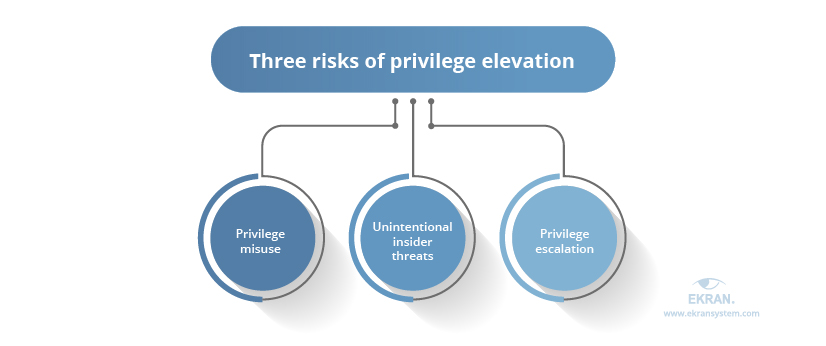
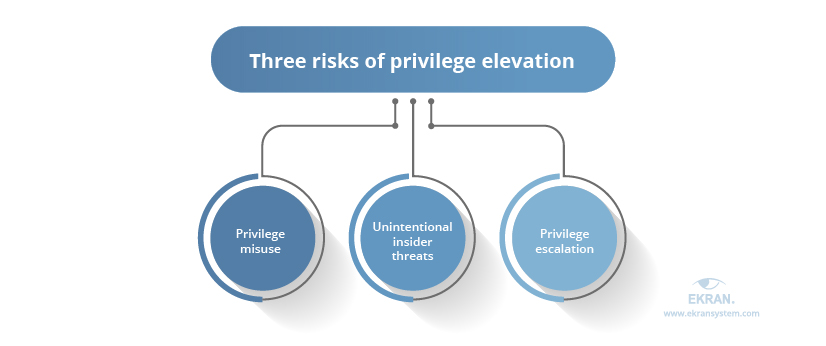
The first issue is privilege misuse, which means using legitimate access for an illegitimate purpose. Malicious insiders can intentionally use their elevated privileges to steal or compromise sensitive corporate data, often aiming to profit from reselling valuable information.
Secondly, there’s a risk of unintentional malicious insider threats. Privileged users can harm an organization’s critical systems by mistake. For example, they may accidentally delete files or make modifications to a sensitive system.
The third risk is privilege escalation, which refers to gaining elevated access rights illegally. Escalation of privileges is often performed by malicious insiders who exploit bugs, design flaws, or configuration errors in an application or system to get privileged access rights. Another example of privilege escalation is an attack by external intruders who hack regular accounts.
You can read more about malicious insiders and privilege misuse in our other blog articles on those topics. For now, let’s explore the issue of privilege escalation in detail. Privilege escalation can be executed in two ways: horizontally or vertically.
Horizontal privilege escalation is when users leverage their current access permissions to compromise other user accounts with the same level of access. Thus, while not elevating their overall access level, malicious actors can get a hold of data that’s available only to other employees.
Vertical privilege escalation allows users to access accounts with higher privileges. It’s more dangerous than horizontal privilege escalation, as malicious insiders may use vertical privilege escalation to gain access to root accounts and execute malware, erase files, and disrupt valuable data.
To better understand the importance of efficient privilege management, it’s essential to know the consequences of uncontrolled or thoughtless privilege elevation.
8 Best Practices of Privileged User Monitoring
Consequences of uncontrolled privilege management
How efficient is your privilege management?
When provided thoughtlessly, additional permissions may compromise your cybersecurity. Malicious insiders may abuse privileges and leave your organization with severe issues such as the following:
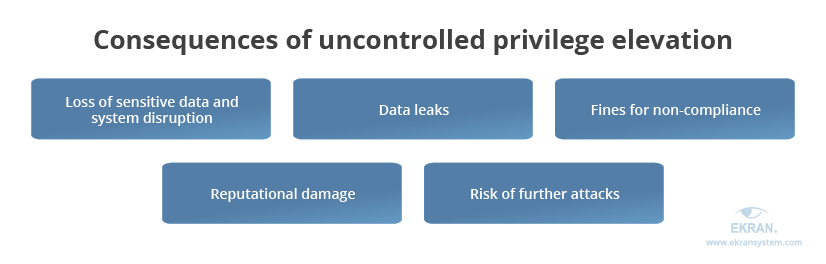
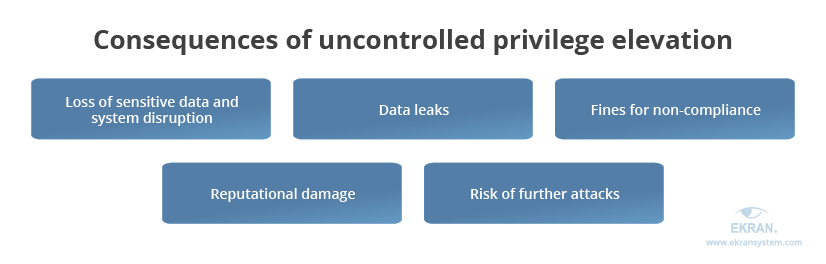
- Loss of sensitive data and system disruption. It takes a significant amount of time and effort to restore system configurations and files and fix issues caused by privilege abuse.
- Data leaks. Privilege abuse often leads to cybersecurity incidents involving the leaking of personal information of employees and customers as well as confidential business information.
- Charges for not complying with security standards and regulations like GDPR, HIPAA, PCI, and NIST’s compliance standards. Privileged users can change access configurations and security controls, which may lead to violations of compliance requirements.
- Reputational damage. The issues mentioned above may harm an organization’s reputation, casting doubts on its security and integrity among potential customers and partners. This is especially true if incidents lead to lawsuits regarding data leaks that concern employees or customers.
- Risk of further attacks. Privilege escalation can be a preparation for a more specific and severe attack on your critical systems, especially if insiders manage to get access to accounts with the highest set of permissions. Intruders can modify your security settings, inject malicious code, and do much more.
Uncontrolled privilege elevation can cause severe damage to an organization’s reputation, security, and performance. The best way to mitigate such incidents is to prevent them right off the bat. Let’s explore several tactics that will secure your sensitive data from malicious insiders with elevated privileges.
Privileged Access Management vs Privileged User Management: What’s the Difference?
How to efficiently manage user privileges
Prevent cybersecurity incidents instead of dealing with their consequences.
As we mentioned above, accounts with elevated privileges may be at risk because of malicious insiders who misuse their privileges. But negligent insiders can also compromise an organization’s cybersecurity by mistake. That’s why you may consider implementing such measures as cybersecurity awareness training to prevent privileged users from making mistakes.
Efficient privileged user management and privileged account management are essential to secure sensitive data and prevent insider threats and other cybersecurity incidents. Here are several best practices that can help you improve the quality of your privilege management:
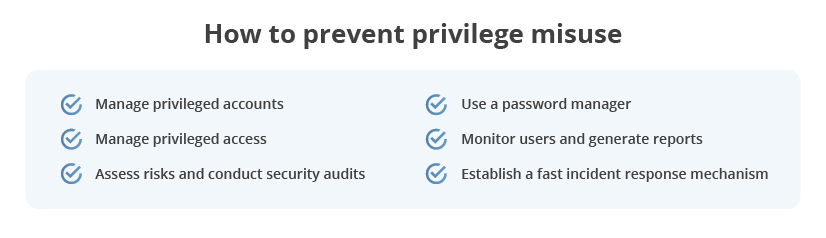
Set up robust privileged account management. Arrange visibility and establish clear rules for using accounts with elevated permissions. For instance, you might decide that privileged accounts must only be used for certain tasks that require elevated privileges and not for ordinary tasks. Additionally, make sure to remove accounts once employees don’t need them anymore or an employee leaves your company, since inactive accounts pose security risks.
Efficiently manage privileged access. Define which users have what access rights. Apply the principle of least privilege and zero-trust model to provide employees with the minimum access they need for their work. You can also try the just-in-time approach, ensuring that privileged access is provided only to authorized users for working with particular systems for a certain amount of time and for a valid reason.
To ensure robust privileged access management, implement reliable authentication and authorization mechanisms. You should also strengthen your user verification with multi-factor authentication (MFA) technology. Consider using one-time passwords to grant privileged access only when needed to perform a certain task.
Types of Two-Factor Authentication
Assess risks and conduct security audits. Regularly scan your systems and applications for vulnerabilities and address any issues immediately. You can also arrange specific testing for privilege escalation to check how easy or complicated it is to gain elevated privileges in your web applications. To secure your corporate network, use reliable risk assessment tools to look at characteristics like performance problems, network-related and user-related issues, and storage issues.
Employ strict password management for privileged accounts. All privileged accounts and credentials must be under centralized management to secure them against access from unauthorized users. To do this, you can apply proven practices like mandating a certain password length and complexity, rotating passwords, and limiting the number of login attempts with a wrong password. Make sure to check requirements for password management in standards, laws, and regulations like NIST 800-63, HIPAA, PCI DSS, and the GDPR.
Secrets Management: Importance, Challenges, Best Practices
Perform comprehensive user monitoring and generate reports. Deploy dedicated software to track and record the activity of regular and privileged users. Consider choosing a tool that gathers information in a forensic format so you can provide evidence to a court in case a security incident occurs.
Implement a fast incident response mechanism. Use detection and response tools to identify an incident as soon as it happens. Configure these tools to receive alerts and notifications once the software detects suspicious activity and block users before they manage to perform malicious actions.
To prevent issues caused by privilege misuse or escalation, organizations should review the current security of their systems and implement best practices of privileged user monitoring and detection mechanisms into their workflows. Dedicated software provides better visibility into the actions of privileged users and allows businesses to spot privilege abuse at its early stages.
Using Ekran System for privilege management
The privileged user management solution provided by Ekran System allows you to control and monitor privileged users, avoiding the risk of insider threats. With privileged access management functionality, you can enhance your network’s protection using multi-factor authentication, one-time passwords, and personalization of shared accounts.
Ekran System helps you efficiently manage all access rights with password management functionality. You can grant and restrict permissions as well as deliver temporary credentials for allowed sessions via the secure password vault.
You’ll also benefit from incident response functionality to detect suspicious activity and prevent cybersecurity incidents. You can set targeted alerts and specific rules for automatic responses, or manage individual cases manually.
Furthermore, each session initiated by a privileged user can be carefully recorded and audited in Ekran with the help of multi-parameter search, filters, and various tools for investigations and forensics.
Finally, Ekran System helps you ensure compliance with SWIFT CSP, SOX, PCI DSS, HIPAA, GDPR, NIST 800-53, and other standards, laws, and regulations.
Privileged User Monitoring and Auditing for a US-based Financial Services Company [PDF]
Conclusion
Some employees require elevated privileges to perform their tasks. However, when privileges are granted without proper oversight it can lead to lots of cybersecurity risks. Elevated privileges may be misused by malicious insiders or abused by external cybercriminals, leading to data loss and reputational damage.
Secure enterprise data by implementing the best practices mentioned in this article. It’s essential to manage privileges within your organization in order to secure critical data from malicious insiders, negligent insiders, and intruders.
With Ekran System, you can detect insider threats across your organization and mitigate the risk of privilege elevation before it leads to a cybersecurity incident and loss of reputation. Set up the free 30-day trial version of Ekran System and see how Ekran can enhance the protection of your corporate network.





