Integration with Microsoft Power BI
Visualize data. Get cybersecurity insights. Focus on what matters to your business.
Use data analytics to improve employee productivity and mitigate insider risks
Data is power. But modern cybersecurity solutions collect too much data for humans to analyze it and get actionable insights. Real-time dashboards, security alerts, and user session records help you detect and stop any suspicious activity. And with business intelligence, you can see a high-level picture of the state of your cybersecurity.
Microsoft Power BI analyzes and structures data arrays collected by other software. When integrated with Ekran System, Power BI can easily export and visualize data on employees’ idle and work time as well as productivity; it can also provide you with insights on common applications and URLs that your employees access.
Such business intelligence allows you to detect long-lasting issues with employee productivity and indicators of possible security violations.
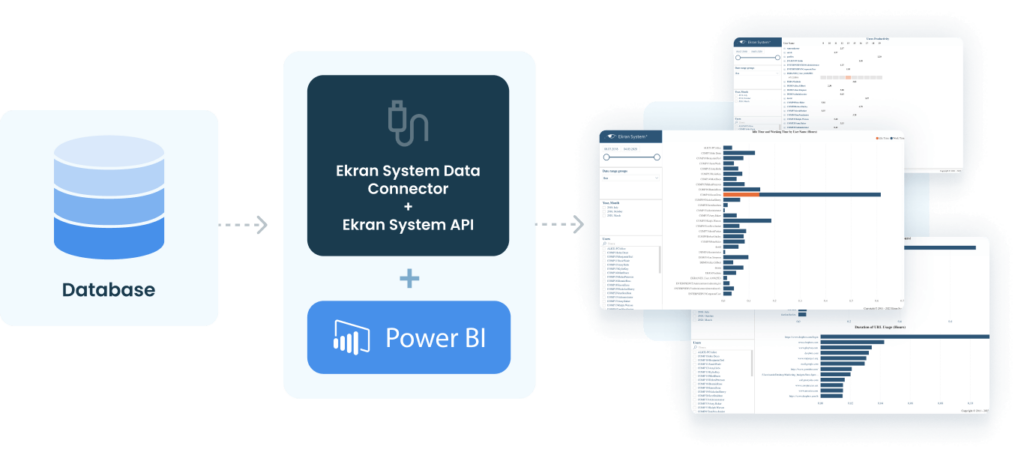
Create a seamless data pipeline
To help you import monitoring data into Microsoft Power BI, we enabled the Ekran System Data Connector to create a data pipeline between the two solutions. You only need to add the Ekran System API key and endpoint name to Microsoft Power BI and specify the time period for the data you want to analyze.
After a couple of clicks, you’ll have three custom business intelligence reports that will be updated with new data automatically. Our integration allows you to use Microsoft BI’s flexibility and configure these reports however you want — the needed data is all there.
Microsoft Power BI reports
Ekran System integrations
Ekran System employee tracking software seamlessly integrates with your infrastructure, including with leading SIEM and ticketing systems.

Recommended resources
Let’s get the conversation started
Contact our team to learn how our insider risk management software can safeguard your organization’s data from any risks caused by human factors. Book a call with us at a time that suits you best, and let’s explore how we can help you achieve your security goals.