
Privileged User Management and Monitoring
Minimize the risks posed by your privileged users with Ekran System’s user activity monitoring, access management, and incident response functionality. ALL-IN-ONE

Protect your organization from privileged user risks
Privileged users and their accounts are considered one the most critical assets in your organization’s security. Here’s why:
Access to the most sensitive data and systems
Fewer cybersecurity controls
Easy to act on malicious intent
High price of human error
Privileged users know the ins and outs of your systems and can abuse their privileges without being noticed. Privileged accounts are also the primary targets for external attackers. Intruders who have access to privileged accounts can easily bypass security precautions and hide any traces of malicious activity.
The number of insider threats keeps rising
74% of organizations say insider attacks have become more frequent
2023 Insider Threat Report by Cybersecurity Insiders
The average cost of a single insider threat increased by 85% between 2016 and 2022
$645,997 total average cost of a single insider threat incident in 2022
2022 Cost of Insider Threats Global Report by the Ponemon Institute
Create and maintain an actionable system for monitoring and controlling privileged users – the most powerful insiders in your infrastructure. Ekran System is the perfect solution for this challenging task.
Benefits of privileged user management
with Ekran System solution
Get complete visibility into your network, systems, and users’ actions to make informed decisions about security and risk management.
Prevent cyberattacks and data breaches by detecting potential security threats, including insider activity and external attacks on privileged accounts.
Detect unauthorized access, changes to system configurations, and misuse of resources to improve security and prevent future violations.
Record all privileged user activity to deter inappropriate behavior and provide evidence in case of an incident.
Meet HIPAA, PCI DSS, GDPR, and other requirements to reduce the risk of fines and legal repercussions.
Know for sure who does what inside the corporate IT perimeter and secure your organization’s resources with robust employee activity monitoring and screen recording.
Control insider risks with Ekran System’s privileged user management
Privileged access management
Get full visibility over all of your privileged and regular users and control their access permissions with Ekran System’s privileged access management system. Use manual access approval to granularly configure who can access what and when. Boost your network’s protection by integrating the Ekran System platform with your internal ticketing system.
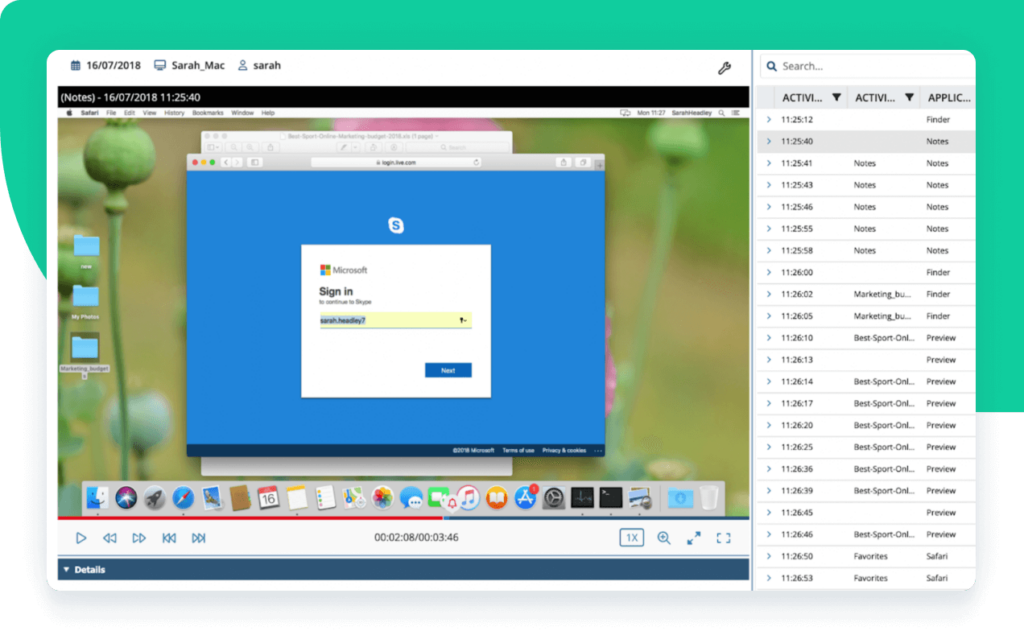
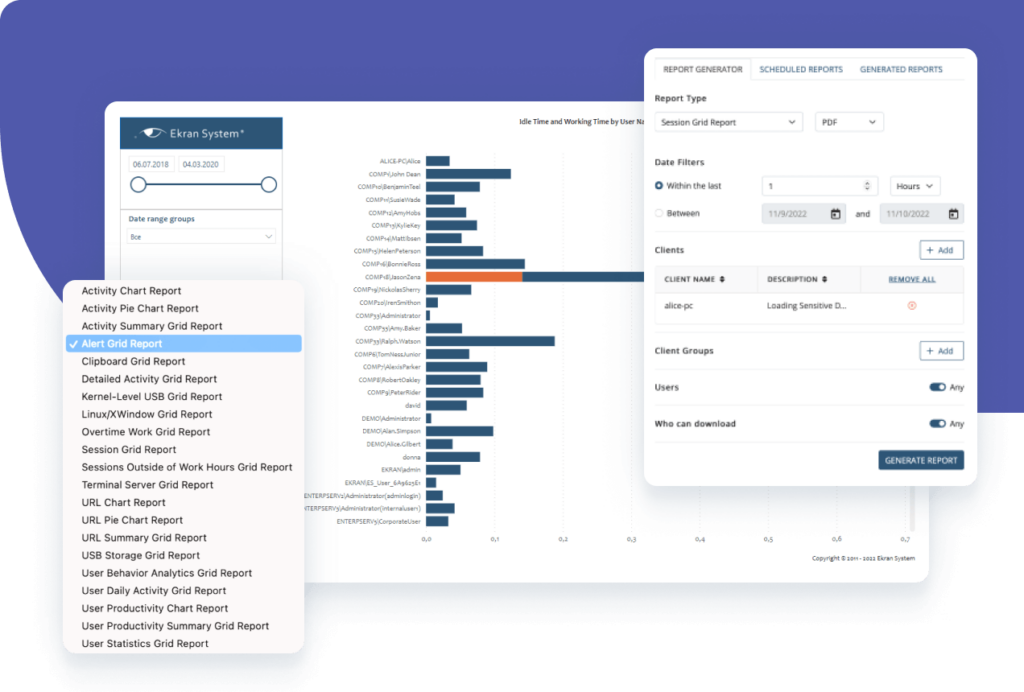
Privileged user activity audit
Leverage Ekran System’s privileged user activity monitoring system to record every session and get useful insights about each user action. Use multi-parameter search, filtering, and reporting for a convenient and focused auditing process. Obtain an audit trail of all administrative activity in Ekran System and make sure no one can tamper with it. Ekran System’s privileged user activity auditing capabilities allow you to export monitored data for forensic investigations if needed.
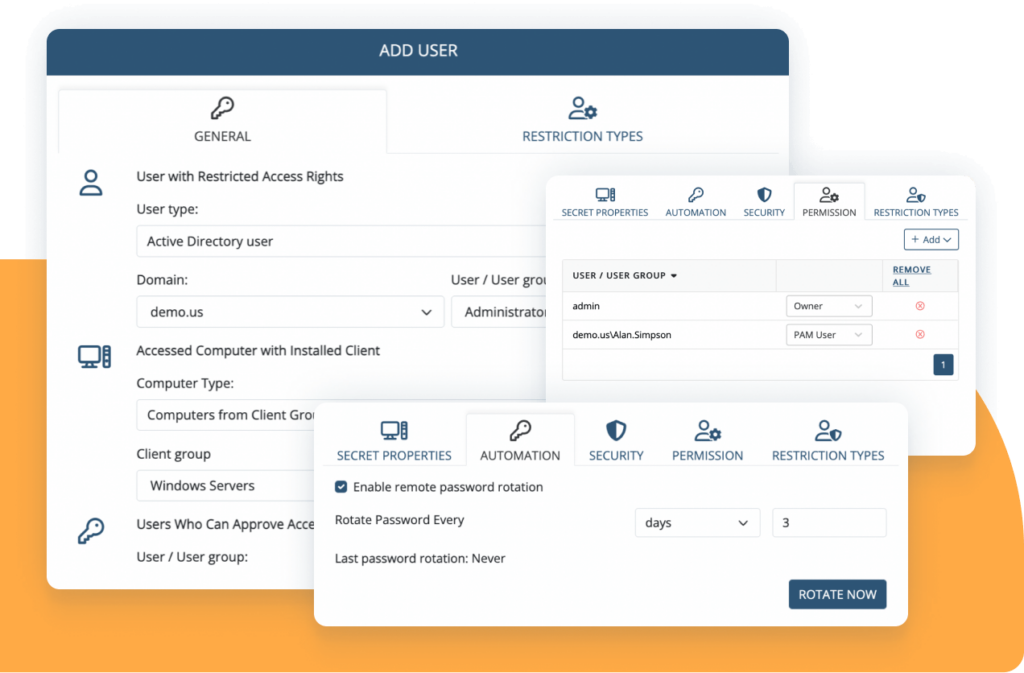
Privileged account and session management
Get full control over sessions initiated from your jump servers, and restrict or grant account access permissions. Deliver temporary credentials for allowed RDP sessions via the secure password vault. Secure privileged accounts with two-factor authentication, one-time passwords, and personalization of shared accounts.
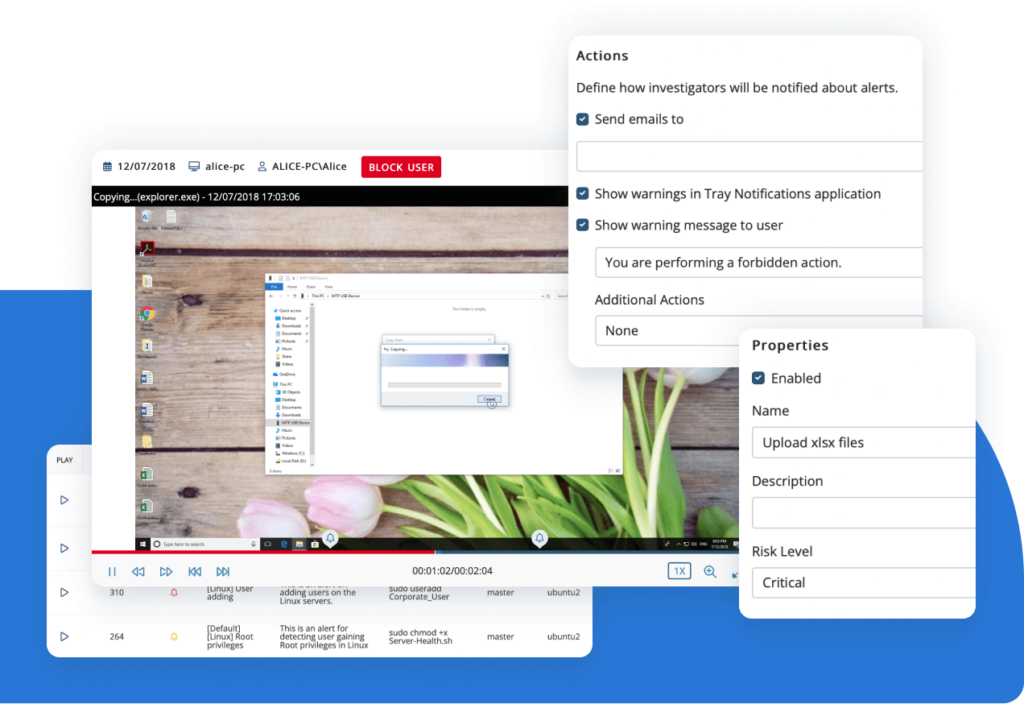
Real-time incident response
Quickly and effectively respond to security threats with Ekran System’s customizable alerts. Respond to incidents and suspicious activity manually, or set automatic responses. Use a live session view to see what’s actually happening in your environment.
Supported platforms
Monitor user activity with Ekran System®
Get more with enterprise-grade insider threat detection software
Visually structured evidence trail resulting in low incident response time
Context-rich recordings significantly reduce CERT and SOC response times. One-click search across suspicious activity makes investigations faster and more effective.
AI-based compromised account detection
Cybercriminals are constantly improving their ways of compromising privileged accounts. Powered by artificial intelligence, the Ekran UEBA system can detect a hacker who has penetrated a corporate system using stolen credentials.
Lightweight software agent and highly optimized formats for storing data
The lightweight agent works silently and isn’t noticeable to users or other programs. Collected data is saved in searchable and highly optimized video, audio, and text file formats for compact log storage and easy reporting.
Active in your environment in 20 minutes or less
Ekran System is quick to install and easily integrates with SIEM and ticketing systems. You’ll get a ready-to-use solution right after a coffee break.

Learn how Ekran System assists our customers in continuously preventing threats coming from the inside.
What our clients say about Ekran System’s insider threat prevention tools
Case studies
FAQ
A privileged user has elevated access rights to an organization’s critical systems and sensitive information. Common examples of privileged users are system administrators, C-level executives, and human resource managers. Ekran System monitors the activity of both privileged and common users for better protection against insider risks.
Privileged account management refers to the processes and technologies used to manage and secure privileged accounts that have access to an organization’s critical systems or sensitive data. Privileged account management capabilities of Ekran System include measures such as user activity monitoring, access management, password management, and other processes to secure privileged accounts.
Privileged activity monitoring is critical to:
- Minimize insider threats
- Prevent unauthorized access to sensitive information and critical systems
- Comply with cybersecurity requirements
- Ensure user accountability
Organizations can monitor privileged user activity using comprehensive privileged user management solutions like Ekran System. Ekran System monitors users in real time and records an audit video trail of privileged user activity, including an array of metadata: typed keystrokes, visited URLs, launched applications, and more.
Yes. Privileged user management solutions like Ekran System enable monitoring and recording of privileged user activity across multiple devices and platforms, including Windows, Linux, and macOS. You will be able to monitor the activity of all users on all endpoints and servers that have the Ekran System Client application installed on them.
Privileged password management is the practice of securing and managing the credentials of privileged accounts. You can use Ekran System’s password management capabilities to secure privileged account credentials, automate password rotation and management, and set your own access request and approval workflow.
Blog spotlight
Let’s get the conversation started
Contact our team to learn how our insider risk management software can safeguard your organization’s data from any risks caused by human factors. Book a call with us at a time that suits you best, and let’s explore how we can help you achieve your security goals.











