Remote and hybrid work models have transformed how organizations operate, offering flexibility, cost efficiency, and other benefits. However, this shift also introduces challenges, particularly in securing sensitive data against breaches and maintaining employee productivity. Remote employee monitoring has emerged as a vital solution to address these concerns.
In this article, we will explore the risks of remote work and how to manage these risks with actionable practices. You will also discover how to monitor employees working from home without violating user privacy.
What is remote employee monitoring?
Remote employee monitoring is the practice of tracking the activities, performance, and behaviors of employees who work remotely. You can monitor employees working from home using specialized software to get insights into employee productivity, check adherence to schedules, and manage security risks.
The COVID-19 pandemic revolutionized the workplace, and today more organizations work remotely or in a hybrid setting, which has further accelerated the desire for many employers to implement employee monitoring practices.
Gartner, How Employee Productivity Monitoring Has Evolved – And What’s Next for HR
To effectively analyze employee productivity and security risks, various user activity monitoring tools may be used to track different aspects of remote user activity, including:
- Website and application usage — Detecting which URLs and applications employees access during work hours.
- Time spent on work — Measuring the amount of time users spend on specific tasks and work in general.
- Keystroke monitoring — Tracking what employees type, copy, and paste during their everyday work activities.
- Screen activity — Monitoring and recording what users do on their screens for in-depth analysis when reviewing specific actions.
- Behavioral patterns — Leveraging AI to analyze patterns in remote employee behavior for detecting potential security threats or productivity issues.
That being said, before applying remote employee monitoring practices, consider why you need to implement them in the first place.
Why should you monitor employees working from home?
Remote connections to your systems can become a threat if not protected properly. As remote employees access sensitive data from outside traditional cybersecurity perimeters, this data is more vulnerable to external threats.
Common concerns and risks of remote work
To minimize both external and internal attacks, you should be aware of the common risks and concerns posed by remote employees:
Common concerns and risks related to remote workers
Using public Wi-Fi networks
Using personal devices for work
Lack of cybersecurity awareness
Susceptibility to social engineering attacks
Poor password protection
Using outdated software
Malicious manipulation of data
Slacking off
Using public Wi-Fi networks
No authorization is required to connect to public Wi-Fi, so hackers can hijack data a remote user sends via these unsecured connections. Such data could include anything from work-related emails to sensitive corporate information and user credentials.
Using personal devices for work
Personal devices often lack the security defenses found on corporate workstations, such as antivirus software, firewalls, and encryption algorithms, leaving them vulnerable to cyberattacks. Moreover, personal devices are frequently shared among family members, increasing the risk of accidental exposure to sensitive work data or the installation of malicious software. Therefore, it is strongly recommended to provide employees with corporate devices that have been pre-configured with security tools in place.
Lack of cybersecurity awareness
Remote employees should be trained in basic cybersecurity practices and their importance. Without such knowledge, they’re likely to ignore security measures to make their work faster and more comfortable. For example, some employees neglect to use VPNs, even though their company has provided them, or fail to recognize malicious emails.
Susceptibility to social engineering attacks
Telecommuters rely heavily on digital communication, which makes them prime targets for phishing and other social engineering attacks that manipulate them into revealing confidential information. The physical separation from colleagues and IT teams increases the risk, as remote workers may lack immediate access to in-person support or second opinions.
Poor password protection
Weak password management is another recurring issue in remote work setups. Stealing credentials from remote employees is easier than from on-site employees due to the extended attack surface. Moreover, organizations may fail to enforce additional authentication measures for accessing their systems.
Using outdated software
Employees sometimes neglect to update their software regularly. Updates take time, cause disruptions, and require workers to get used to the new version. However, when remote employees fail to update their security software routinely, hackers can perform successful attacks by abusing known software vulnerabilities.
Malicious manipulation of data
Though remote employees often have the same level of access as their on-site colleagues, they’re usually less supervised by the IT security team. Therefore, it’s easier for teleworkers to conduct insider attacks which may involve privilege abuse, data theft, espionage, and other types of malicious activities.
Slacking off
Although most employees are productive both in and out of the office, some may find it difficult to focus on work tasks while at home. Such employees can become distracted by cleaning, browsing the news, playing games, etc. Without dedicated remote employee monitoring software, it may be difficult to evaluate if a person is working efficiently.
Now that we know the common concerns of remote work, let’s see how employee monitoring can help.
Benefits of remote employee monitoring
Remote employee monitoring can significantly minimize the risks mentioned above. With effective remote work monitoring measures in place, you can:
Advantages of remote employee monitoring
Enhance accountability
Enable crisis response
Improve overall security posture
Allocate resources efficiently
Ensure IT compliance
Increase employee productivity
Enhance accountability
Monitoring solutions can help you see who does what within your network and provide a record of remote user activity, promoting accountability in adhering to security protocols. If an insider incident occurs, you can reconstruct the chain of events and see who’s responsible by reviewing user activity. Remote work monitoring also helps managers track individual contributions to team goals.
Enable crisis response
During emergencies such as a security breach, monitoring software provides real-time insights into system usage and remote employee activity. Monitoring can help your organization quickly identify and resolve issues, minimizing disruptions. You can also use the records of malicious user actions to investigate the incident and take precautions in the future.
Improve overall security posture
By monitoring work-from-home employees, you can identify security threats such as unauthorized access, use of forbidden applications, or sharing of sensitive information. Based on insights into user activity, you can mitigate risks to strengthen your organization’s ability to prevent data breaches and other cybersecurity incidents.
Allocate resources efficiently
The insights provided by employee monitoring software enable you to see areas where employees are being underused or overwhelmed by their workloads. Thus, you can reallocate personnel to where they are most needed, optimizing operational efficiency.
Ensure IT compliance
User activity monitoring compels remote users to adhere to your IT security policies, such as using authorized devices, VPNs, and secure networks. This, in turn, helps you comply with cybersecurity laws and regulations such as the GDPR, HIPAA, and NIS2. Some regulations even list user activity monitoring itself as a requirement.
Increase employee productivity
Some user activity monitoring tools allow you to track the time spent on tasks, which can help you detect inefficiencies and offer support or training to specific employees. Additionally, monitoring helps remote employees to stay focused, as they are less likely to give in to distractions when they’re aware of the ongoing monitoring process.
Implementing cybersecurity and remote worker monitoring best practices can mitigate risks and concerns about telecommuting. Let’s review some time-tested methods for securing the actions of remote employees.
Best practices for monitoring and securing remote work activities
We’ve prepared a list of best practices to help you monitor and secure remote activities. Some are purely organizational, while some require a dedicated remote employee monitoring system.
Monitoring and securing remote work activities
1
Create a remote access policy
2
Educate your employees
3
Secure and limit remote access
4
Protect user credentials
5
Monitor remote user activity
6
Track employee productivity
7
Anonymize personal data
8
Streamline incident detection and response
1. Create a remote access policy
A remote access policy is a formal document outlining how remote access is established and secured in your organization. You can make it a part of a general data security policy. Include the following in your remote access policy:
- A list of security software and access control measures
- Instructions for telecommuters on how to connect to your network
- Measures for protecting remote user credentials
- Conditions for providing and revoking employees’ remote access
- A description of how certain remote access activities are monitored
- Rules for securing personal devices used for remote access
Make sure your employees can access this policy at all times.
2. Educate your employees
Maintaining cybersecurity awareness among your remote employees is vital yet some organizations overlook it. Conduct regular training sessions explaining the key concerns and risks of telecommuting we’ve outlined, and how to address them. Pay special attention to educating your remote employees on how to detect phishing emails and other social engineering attacks. You can simulate these attacks to make training hands-on and engaging while evaluating the readiness of your employees to spot real-life attempts.
It’s also crucial to educate your employees about the importance of remote workforce activity monitoring. Clearly explain the scope and the purpose of your monitoring practices to promote trust and transparency.
3. Secure and limit remote access
Due to the susceptibility of remote workers to account compromise and other cyberattacks, protecting their access to your IT infrastructure is critical. The use of VPNs, encrypted connections, and secure remote desktop protocols can safeguard data in transit. As for more advanced measures, consider implementing a zero trust architecture, enforcing strict access controls, and using multi-factor authentication (MFA) to ensure users are authenticated, authorized, and verified before accessing your resources.
Implementing dedicated access management software helps simplify and enforce your security policies. Syteca is a comprehensive cybersecurity platform featuring robust privileged access management (PAM) and user activity monitoring (UAM) capabilities. Syteca PAM enables your organization to:
- Secure and provide granular remote access to your organization’s endpoints
- Provide temporary access for external users
- Verify user identities with two-factor authentication (2FA)
- Discover and onboard privileged user accounts
4. Protect user credentials
Enforcing strong password policies is a vital step in securing remote credentials. These policies include requirements for password complexity, password rotation, and the use of password management tools. Password managers can help your organization take control of, secure, and automate password provisioning for both remote and in-house employees.
Syteca offers robust workforce password management capabilities, allowing you to:
- Manage secrets without revealing passwords to remote users
- Implement automated password rotation
- Secure passwords in an encrypted vault
- Enable SSH key management
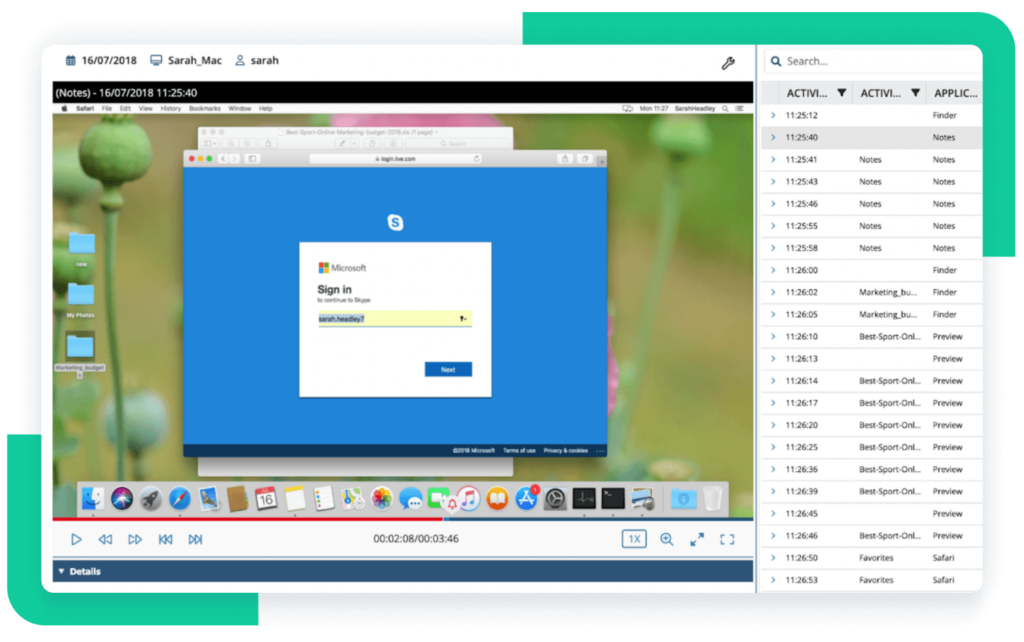
5. Monitor remote user activity
A user activity monitoring software solution lets you get the most context possible about remote user activity in your infrastructure. Track user activity like login times, applications used, and URLs visited to detect suspicious behavior, enforce compliance with security policies, and generate audit logs for investigations or reporting.
Syteca UAM allows you to monitor remote work sessions in your IT environment, enabling you to:
- Monitor RDP sessions connected to your endpoints
- Track and record on-screen user activity in real time
- Search a particular session for specific typed keystrokes, visited URLs, launched applications, and more
- Generate convenient reports on user activity
6. Track employee productivity
Productivity monitoring tools assess how employees use their time by tracking application usage, task completion, and idle periods. By monitoring your remote workers’ productivity, you can pinpoint inefficiencies, improve processes, and allocate resources effectively to streamline your organization’s overall performance.
Syteca’s reports and dashboards allow you to monitor remote employee productivity by providing visual insights on various aspects of user activity, including:
- Total active vs. idle time
- Top applications used
- Top websites used
- User productivity level
7. Anonymize personal data
Engage in how to monitor remote employees ethically. Protect the privacy of your remote workers by anonymizing personal data wherever possible. For example, some productivity metrics can be shared without identifying specific individuals. Anonymization helps balance security with ethical considerations and comply with data privacy regulations such as the GDPR and CCPA.
Syteca protects user privacy with its advanced data pseudonymization feature, enabling you to:
- Mask employees’ personally identifiable information during monitoring and recording
- De-anonymize the hidden personal information upon request if an investigation is needed
8. Streamline incident detection and response
Develop an incident response plan as an emergency guideline with predefined steps for containment, investigation, and remediation of cyber threats. Combine your organizational measures with an automated system that detects unusual activity such as unauthorized access or data transfers.
Syteca UAM includes a comprehensive system of user activity monitoring alerts, which provides your security team with the means to:
- Receive real-time notifications on suspicious user activity and security events
- Automate responses to threats: block users, terminate processes, or warn policy breakers upon triggering alerts
- Integrate user activity data with an SIEM system
Case study
An HVAC Service Provider Secures Data and Maintains Employee Productivity after Switching to Remote Work

Conclusion
Monitoring remote workers is essential for organizations with remote and hybrid office environments. It enables your organization to secure sensitive data, maintain regulatory compliance, and ensure operational efficiency by offering valuable insights into employee productivity and potential security risks.
In addition to implementing the best practices we have provided, you can deploy dedicated employee monitoring software to streamline your efforts. The Syteca platform allows you to verify user identities, manage remote user access, monitor user activity, respond to incidents in real time, and much more.